Why More and More Enterprises Are Building Private CDNs
For the past decade, public CDNs have been the default choice for almost all internet businesses. They addressed the primary challenge of global content distribution with an extremely low barrier to entry. However, as system complexity, access scale, and compliance requirements continue to escalate, the limitations of this model are becoming increasingly apparent: unpredictable cost models, a lack of customization capabilities at the edge, and opaque data paths.
In a growing number of scenarios, the edge is no longer merely a “transport layer.” Instead, it has evolved into a critical node for running business logic, executing security policies, and delivering user experience. Continuing to rely on external platforms in such situations means that critical capabilities and risk control remain in the hands of third parties.
This article aims to address a pressing question: when an enterprise’s edge requirements surpass the capabilities of traditional CDNs, how can they reliably build their own private CDN infrastructure? We will explore how a modern platform like OpenResty Edge can enable this crucial transition, allowing enterprises to reclaim control, speed, and cost efficiency.
In the early stages of enterprise development, public CDNs are indeed an efficient and practical choice. They solve the problem of global distribution with a very low barrier to entry—simple, stable, and cost-effective. However, as business complexity and traffic volume grow, more and more enterprises are discovering that: the growth curve of CDN costs is outpacing the growth curve of business.
When “Commoditized Services” Undermine Innovation
For many companies, CDN is no longer a negligible expense but a continuously expanding expenditure. What was once an elastic cost model has gradually evolved into an “invisible burden” that fluctuates with traffic. More importantly, the issues stemming from this reliance are not limited to the costs themselves:
- Financially: Edge traffic costs scale linearly with business expansion, making it difficult to achieve economies of scale.
- Technically: The vendor’s closed “black box” architecture prevents teams from implementing more flexible logic and optimization strategies at the edge layer.
- Security and Compliance: When data paths and execution environments lack transparency, it becomes challenging for enterprises to answer a critical question—“Where exactly does our data go?”
As the edge increasingly becomes the core node for business logic, security policies, and user experience, continuing to rely on public CDNs as a rented service means that critical control points remain in the hands of others.
Four Inherent Challenges of Public CDNs
As businesses scale nationally and globally, four major challenges in the content delivery network (CDN) landscape are becoming increasingly evident:
| Solution | Control & Flexibility | Cost Model | Performance Predictability | Security & Compliance | Innovation & Iteration Speed |
|---|---|---|---|---|---|
| Public CDN | Low (Black Box) | Operating Expenditure (OpEx), Pay-as-you-go | Medium (Shared Resources) | Limited (Dependent on Vendor) | Slow (Limited by Platform) |
| Cloud Vendor Edge Nodes | Medium (Limited API/Configuration) | OpEx, Tiered Billing | Medium-High (Limited Resource Isolation) | Medium (Provides Basic Services) | Medium (Dependent on Platform Updates) |
| Rudimentary Self-built (Nginx + Script) | High | Capital Expenditure (CapEx) + High OpEx | Low (Dependent on Team Capability) | Extremely Low (Needs to be built from scratch) | Extremely Slow (Reinventing the wheel) |
| OpenResty Edge | High (Programmable Architecture) | CapEx + Controllable OpEx | High (Exclusive Resources + Tunable) | High (Customizable Security Policies) | Extremely Fast (EdgeLang / Lua) |
Limited Control, Restricted Customization While public CDNs offer considerable flexibility at the configuration level, they remain constrained by the functional boundaries set by vendors. When enterprises require more advanced logical customization for caching strategies, routing algorithms, or security validation, these “configurable options” quickly become a hard limit. For industries sensitive to data sovereignty and compliance, such as finance, healthcare, and government, architectures that restrict deep customization mean an inability to rapidly respond to complex or localized business demands.
Unpredictable Performance and Stability Although public CDNs typically offer SLA commitments, these SLAs often represent “global average” metrics and cannot guarantee stability for specific regions, specific times, or particular business flows. For high-concurrency applications, popular content, or low-latency-sensitive services, the shared node model can still experience congestion or rate limiting during traffic peaks. Enterprises often lack the ability to independently intervene or optimize scheduling strategies, which leads to a lack of predictability and control over overall performance in critical scenarios.
High Bandwidth and Distribution Costs The pay-as-you-go billing model means that the more traffic you have, the more expensive it gets, essentially penalizing growth. Some companies attempt to build their own reverse proxies or small distribution systems, but they struggle to balance performance optimization with operational and maintenance (O&M) costs.
Data Security and Privacy Compliance Pressures With the strengthening of regulations like GDPR, HIPAA, and various localized laws, enterprises not only need to record logs but also require complete visibility into data flow paths and processing boundaries. While public CDNs provide basic access auditing, the underlying data routing, cache locations, and node control remain “unverifiable” black boxes. This turns cross-regional compliance into a significant trust exercise.
In other words, traditional public CDNs, cloud vendor edge nodes, or self-built proxy solutions all struggle to simultaneously address the inherent conflicts across the four dimensions of flexibility, cost, performance, and compliance. This is why more and more enterprises are starting to consider—building their own private CDN.
OpenResty Edge: The Versatile Gateway Built for Edge Computing
So, how does one build a private CDN network that is both powerful and easy to manage? The answer isn’t to reinvent the wheel. You need a platform specifically designed for such scenarios.
OpenResty Edge is precisely such a versatile gateway platform. It’s built upon the globally renowned open-source project OpenResty, but has been carefully productized. Its core mission is to empower enterprises to easily build and manage large-scale, high-performance distributed network clusters, whether serving as a private CDN, API gateway, or application delivery gateway.
Its design philosophy is to simultaneously meet two seemingly contradictory requirements: ultimate ease of use and infinite flexibility.
For daily management and operations teams: You don’t need to be an Nginx or Lua expert. Through the centralized Web console, you can intuitively manage hundreds or thousands of edge nodes, performing most configurations—such as dynamic load balancing, caching strategies, and security rules—all without writing a single line of code or manually modifying configuration files.
For senior engineers seeking ultimate optimization: When you need to implement complex custom logic, you can write specialized rules using EdgeLang—a declarative language specifically designed for edge computing scenarios. These rules are automatically compiled into highly optimized code by the Admin node and securely pushed to gateway nodes worldwide for execution. The visual configurations you see are also fundamentally EdgeLang, ensuring transparency and consistency.
For technical architects who demand complete control: OpenResty Edge offers limitless extension capabilities. You can expand platform functions by writing custom Lua libraries, or even loading your own Nginx C modules, ensuring it can perfectly adapt to your most unique business requirements.
It is precisely this design—“starting with intuitive visualization, mastering code-driven customization, and committed to platform excellence”—that makes OpenResty Edge an ideal engine for building private edge networks. It encapsulates complex underlying technical complexities while fully returning control to you.
Four Pillars for Building a Private Edge Network
Building a private CDN is not to replace existing public services, but to gain higher controllability and certainty on critical paths. This is an architectural upgrade from “platform dependence” to “possessing self-evolution capability”.
The role of OpenResty Edge is not to subvert existing systems, but to provide an infrastructure engine that can gradually take over and deeply integrate, allowing enterprises to gradually establish “controllable, evolvable, and sustainable” edge capabilities while maintaining flexibility.
From Unpredictable Costs to Manageable Assets
The cost structure of public CDNs usually takes traffic and request volume as core billing units, which means business growth will directly translate into continuously increasing operating expenses (OpEx). A healthier technical architecture should enable enterprises to have predictable, measurable, and scalable investment methods in key capabilities.
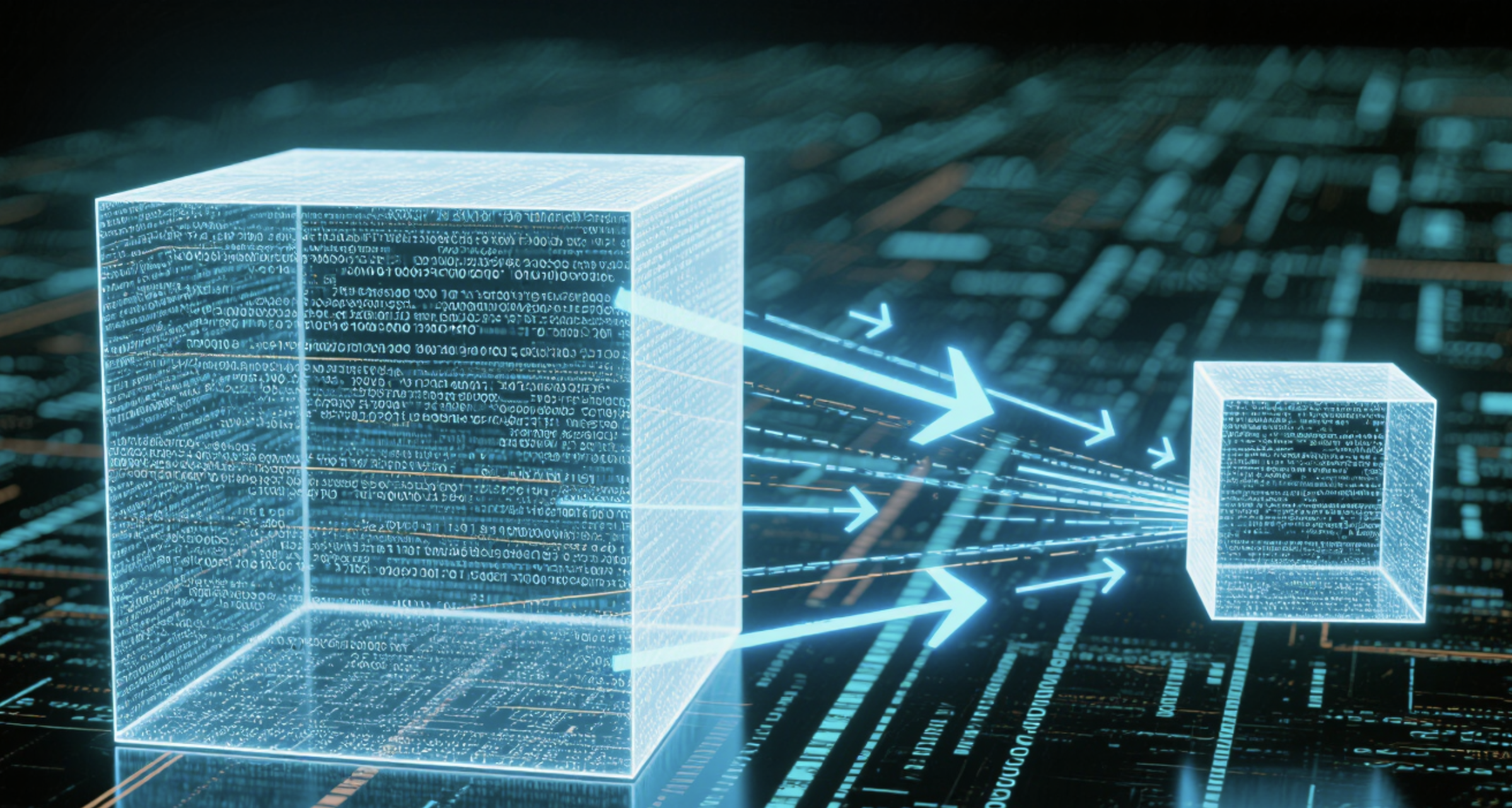
The design philosophy of OpenResty Edge is to transform the edge network from a “leased black-box service” into a “verifiable, configurable proprietary asset.” This asset comprises two core components: globally distributed Edge Nodes (gateway nodes) and the Edge Admin (management node) acting as the central intelligence. Through these, enterprises gain full control over defining and observing network topology, traffic scheduling, and data paths.
The value derived from this “ownership” extends beyond mere cost savings. For instance, when network jitter occurs between the Edge Node serving a user request and the origin server, traditional CDNs typically can only passively await timeouts or failures. In contrast, within a private edge network, you can actively adjust routing strategies based on real-time metrics, enabling more fine-grained adaptive optimization for traffic.
Furthermore, within the private network built by OpenResty Edge, you can customize a multi-layered network topology. This allows edge nodes, following your defined routing logic, to forward requests to “regional core nodes” or “super nodes” with optimized links for tiered origin fetching.
Configurable, observable, and controllable architectural capabilities empower users with genuine command. You can define rules and gain clear visibility into the path, rather than relying on a black box to “make decisions for you.”
User Request → DNS Resolution → Nearest Edge Node → Cache Hit/Origin Fetch → Content Return
↓
Edge Admin Management Node (Configuration Deployment, Monitoring)
More critically, this network is “dynamic.” Through Edge Admin’s unified monitoring and health checks, should any Edge Node fail or experience performance degradation, traffic will be automatically rerouted to healthy nodes, a process entirely transparent to the user.
This is the true essence of asset ownership: it’s not a one-off cost investment, but the construction of a digital infrastructure that is autonomously optimized, self-healing, and continuously generates value. You break free from the passive “traffic tax,” gaining instead a strategic weapon that can be freely shaped according to business needs, and which can fundamentally eliminate bandwidth waste and single points of failure at an architectural level.
At the Edge: Bringing Innovation from Idea to Reality
While backends have been architected with microservices and frontends built with components, the “edge layer” often remains the most inflexible bottleneck in the innovation pipeline. Any new logic or experiment typically requires waiting for vendor interface updates or script approvals.
OpenResty Edge’s mission is to break these shackles. By tightly integrating computing and caching, it transforms the edge from a mere “distribution point” into a powerful “business logic execution platform.” Your business logic can now be executed closer to the user, delivering millisecond responses right where they are.
We offer two powerful “Swiss Army knives”:
- EdgeLang: Our domain-specific language (DSL) is designed specifically for edge environments, featuring extremely concise syntax. Whether you’re implementing canary releases, A/B testing, or personalizing content based on user characteristics, your engineers no longer need complex programming. A few lines of declarative configuration can be quickly deployed.
- Lua Script: For more complex scenarios, we provide access to the full LuaJIT ecosystem. From dynamic request/response rewriting and custom authentication logic to real-time processing of streaming data, it offers unlimited creative space for your senior engineers.
What does this mean for you?
- Image Processing: Eliminate round-trips to the origin. Perform real-time cropping, scaling, and watermarking directly at the edge node, significantly boosting loading speeds and conserving origin server resources.
- Security Checks: Before traffic even reaches your core systems, conduct complex token verification or API protection at the edge, preventing threats from reaching your critical infrastructure.
- User Experience: Deliver different content directly from the edge based on device, geographic location, or membership tier, achieving true personalization.
In the past, these ambitious ideas might have meant weeks of backend development backlog. Now, they can be transformed into global edge rules deployable within minutes. This isn’t just about feature delivery; it’s about empowering your product and engineering teams with a new, accelerated pace of innovation that allows them to outpace competitors. This is the true accelerator of business speed and the genuine source of competitive advantage.
Security and Compliance: Architected into Your DNA
Security and compliance should never be an afterthought. Yet, the inherent nature of public CDN architectures often compels enterprises to trust third parties with their data paths.
OpenResty Edge’s philosophy is “Security Shift Left”:
The Cornerstone of Trust: From “Hope-Based” High Availability to “Engineered” Resilience Service reliability is the foundation of trust. When your business relies on shared public nodes, your availability, recoverability, and control over changes are effectively constrained by third-party infrastructure. OpenResty Edge empowers you to build and control your own self-healing, highly available access network.
- Intelligent Global Server Load Balancing (GSLB): We go beyond basic DNS resolution. You can build the most intelligent traffic routing paths based on multi-dimensional strategies such as user geographical location, IP origin, and even real-time node load (QPS / system load). This ensures users are always directed to the fastest, healthiest node.
- Automatic Failover: Through precise health check mechanisms, Edge can detect and automatically isolate faulty nodes in real-time, seamlessly switching traffic to healthy nodes without any manual intervention. You are no longer a passive recipient of failures, but the architect of your system’s resilience.
The Core of Trust: From “Black Box” Protection to “End-to-End Programmable” Security True security is achieved when policies can be orchestrated as flexibly as code. OpenResty Edge provides a completely transparent, programmable security system covering the entire HTTP application stack, from the entry point to the business logic layer.
- Zero-Cost, Zero-Downtime TLS Management: Through automated Let’s Encrypt certificate application and renewal, or by importing custom certificates, and leveraging live certificate updates, you can easily achieve full-site HTTPS. This eliminates tedious certificate operations and business interruptions caused by updates.
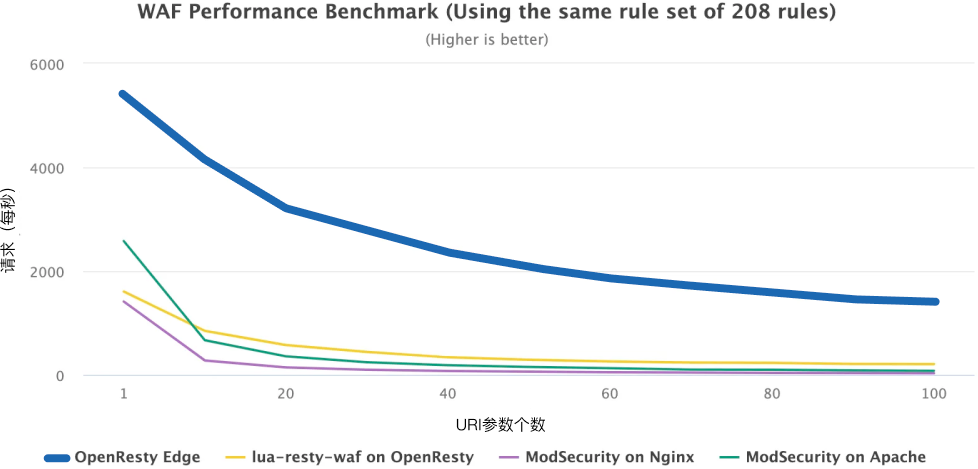
- Programmable Application Layer Firewall: WAF & DDoS protection is no longer about purchasing rigid rule packages. You can flexibly write WAF rules using familiar logic (even EdgeLang / Lua), and configure dynamic rate and concurrency limits, precisely identifying and blocking various threats from CC attacks to SQL injection.
Extension of Trust: From Passive Origin Authentication to Proactive Edge Security Every unnecessary back-to-origin authentication request wastes performance and cost. OpenResty Edge pushes authentication logic to the edge, closer to users, which both enhances user experience and protects your core assets.
- Multiple Built-in Edge Authentication Mechanisms: Whether it’s JWT verification, commonly used in modern applications, or URL signing and expiring URLs to prevent content hotlinking, all can be completed instantly on edge nodes, without burdening the origin server.
- Ultimate Flexibility – Custom Edge Logic: Its most powerful feature is the ability to write fully customized authentication logic using Lua. For example, you can dynamically determine access at the edge based on user membership level, request headers, device fingerprints, and other information. This not only significantly reduces origin server load but also brings your business rules and security policies closer to users than ever before.
In summary, OpenResty Edge enables you to evolve beyond relying on isolated “security products” to a fully auditable, customizable, and programmable secure edge platform. When compliance audits like GDPR and HIPAA require clear documentation of data flow and protection measures, you no longer need to request reports from third parties, because you define and control all paths and rules.
Transform Edge Computing into a Team Accelerator
For edge computing to truly become a team accelerator, the key is not the complexity of the technology stack, but its ability to naturally integrate into existing workflows. An effective platform should reduce the operational and development overhead, and seamlessly integrate with existing CI/CD, monitoring, and configuration management systems, rather than forming new system silos within the team.
Manage the Edge Like Microservices
We empower engineers to flexibly deploy and manage edge logic in environments like Kubernetes, just as they would microservices. This enables robust version control, automated releases, debugging, and one-click rollbacks. By integrating powerful SDKs, WebHooks, and plugin mechanisms, enterprises can deeply embed OpenResty Edge into their existing CI/CD and AIOps workflows. This means:
- No More Black Boxes: Edge policies are transformed from mysterious, operations-exclusive scripts into version-controlled, auditable assets.
- Accelerated Delivery: Product teams can rapidly implement innovative ideas at the edge through streamlined engineering processes, without being constrained by vendor timelines.
Achieve “Zero Blind Spot” Observability: From Firefighting to Foresight
Deploying a private CDN is merely the first step. The true challenge for technical teams lies in ensuring its continuous stability, optimal performance, and sub-second fault localization. OpenResty Edge embeds business continuity-driven observability into the very DNA of its platform.
Out-of-the-Box Real-time Insights: The built-in visual monitoring panel requires no additional configuration. It provides real-time visibility into core business metrics such as traffic, response time, cache hit rate, and status code distribution. When error rates climb or node loads become abnormal, teams can immediately detect risks and nip potential problems in the bud.
Seamless Integration with Your Existing Monitoring Stack: We recognize the significant investment you’ve made in tools like Prometheus, Grafana, or the ELK Stack. Therefore, OpenResty Edge offers flexible log and metric collection mechanisms, natively supporting seamless integration with these mainstream tools. You won’t need to rebuild your monitoring system; simply connect Edge as a new, high-quality data source to facilitate more sophisticated alerting and analysis strategies.
By combining DevOps-friendly automation with end-to-end observability, OpenResty Edge transforms the edge from an elusive “black box” into a completely transparent, controllable, and predictable productivity engine. This not only enhances delivery efficiency but, more importantly, it equips the entire engineering organization with the confidence and capability to master edge operations and drive continuous optimization.
The Edge: Beyond the Network’s Periphery
Today, the edge is no longer merely the network’s periphery. It’s the critical intersection of business experience, security posture, and the pace of innovation. Continuing to outsource it is akin to handing over the keys to your castle to someone else for safekeeping.
Building your own edge network, powered by a modern platform like OpenResty Edge, means securing a future that is financially healthier, more agile in innovation, more reliable in security, and more efficient organizationally.
If you’re interested in how to build a future-proof private CDN network as a one-stop solution, leveraging high-performance architecture, flexible deployment, native edge computing, and DevOps-friendly features, check out the article below: How to build a private CDN with OpenResty Edge.
In practice, OpenResty Edge’s scope of application extends beyond simply replacing public CDNs. It is equally well-suited for deployment in internal enterprise traffic scenarios, acting as an Ingress Controller or a unified entry point for internal gateway layers. This provides consistent policy enforcement and observability for traffic orchestration across multi-cluster, multi-tenant, and multi-environment setups.
Furthermore, at the layer immediately following the ingress gateway, it can assume the role of business-level traffic governance – executing advanced control logic such as canary releases, A/B testing, traffic replication, or latency injection. This layer typically demands extremely high performance, low latency, and precise control. OpenResty Edge’s extensible Lua runtime and distributed management architecture enable these strategies to be executed closer to the business logic with reduced overhead.
From the external edge to internal boundaries, OpenResty Edge provides not just distribution layer capabilities, but a composable, observable, and verifiable traffic control infrastructure. This transforms “the edge” from a passive transmission layer into a unified execution plane that spans the internal and external boundaries of the enterprise network.
What is OpenResty Edge
OpenResty Edge is our all-in-one gateway software for microservices and distributed traffic architectures. It combines traffic management, private CDN construction, API gateway, security, and more to help you easily build, manage, and protect modern applications. OpenResty Edge delivers industry-leading performance and scalability to meet the demanding needs of high concurrency, high load scenarios. It supports scheduling containerized application traffic such as K8s and manages massive domains, making it easy to meet the needs of large websites and complex applications.
About The Author
Yichun Zhang (Github handle: agentzh), is the original creator of the OpenResty® open-source project and the CEO of OpenResty Inc..
Yichun is one of the earliest advocates and leaders of “open-source technology”. He worked at many internationally renowned tech companies, such as Cloudflare, Yahoo!. He is a pioneer of “edge computing”, “dynamic tracing” and “machine coding”, with over 22 years of programming and 16 years of open source experience. Yichun is well-known in the open-source space as the project leader of OpenResty®, adopted by more than 40 million global website domains.
OpenResty Inc., the enterprise software start-up founded by Yichun in 2017, has customers from some of the biggest companies in the world. Its flagship product, OpenResty XRay, is a non-invasive profiling and troubleshooting tool that significantly enhances and utilizes dynamic tracing technology. And its OpenResty Edge product is a powerful distributed traffic management and private CDN software product.
As an avid open-source contributor, Yichun has contributed more than a million lines of code to numerous open-source projects, including Linux kernel, Nginx, LuaJIT, GDB, SystemTap, LLVM, Perl, etc. He has also authored more than 60 open-source software libraries.