Configuring the built-in captcha webpages in OpenResty Edge
Today, I’d show you how to configure OpenResty Edge’s built-in captcha for applications.
Configure OpenResty Edge’s built-in captcha
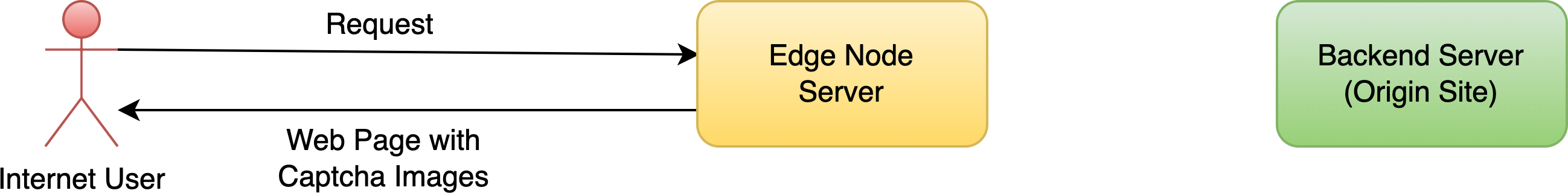
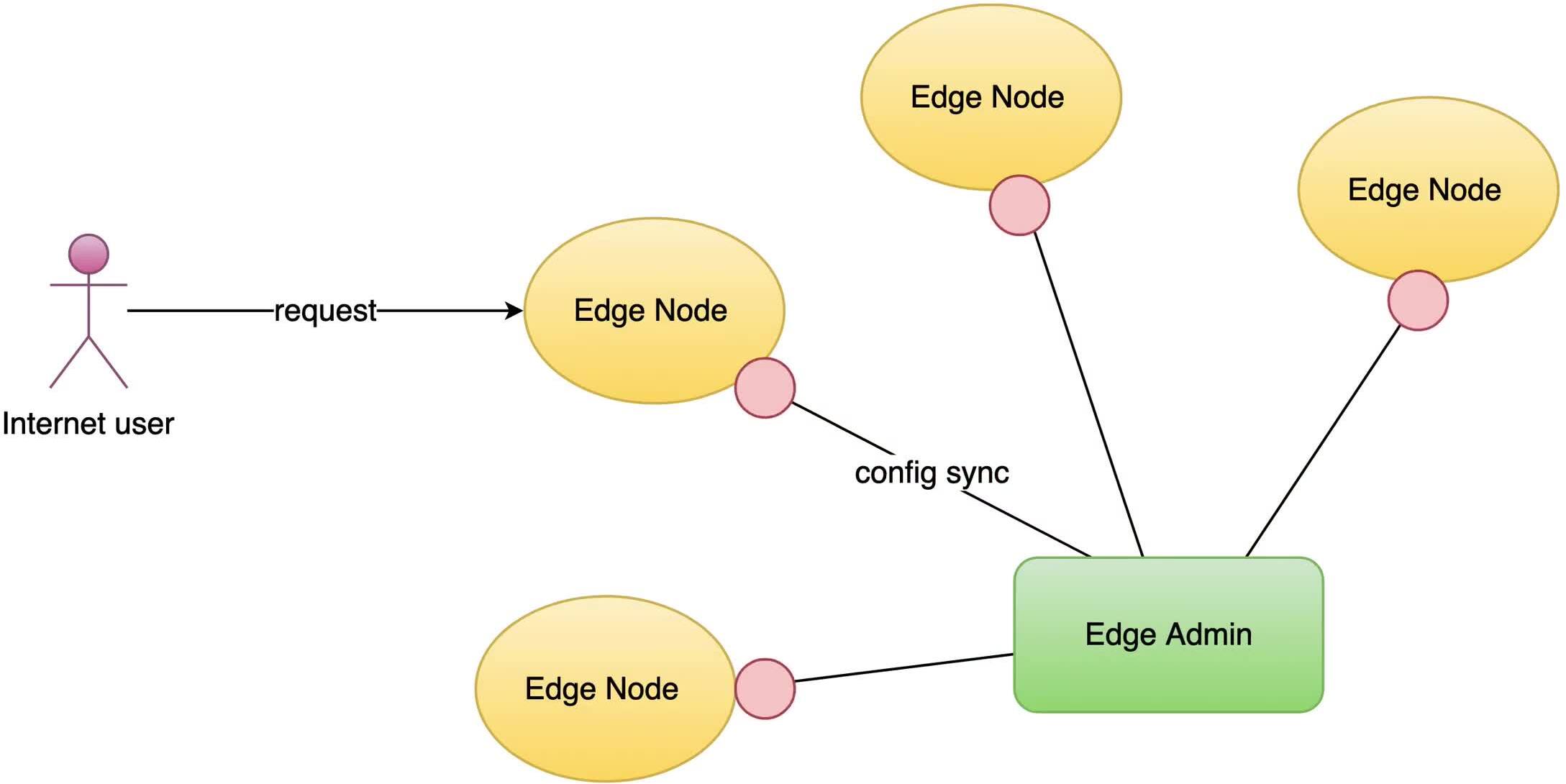
The OpenResty Edge built-in captcha is a captcha response returned directly from the OpenResty Edge gateway server.
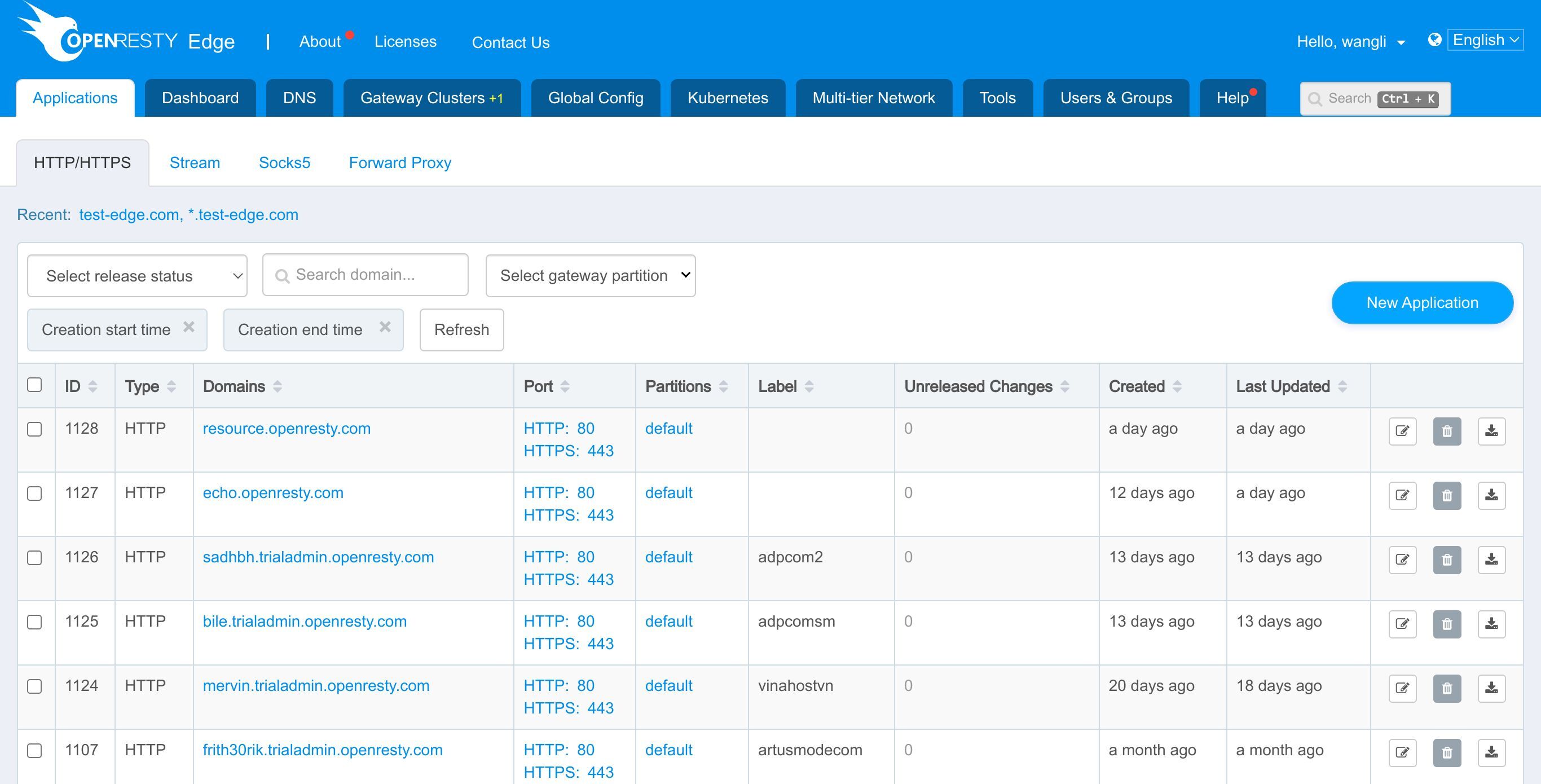
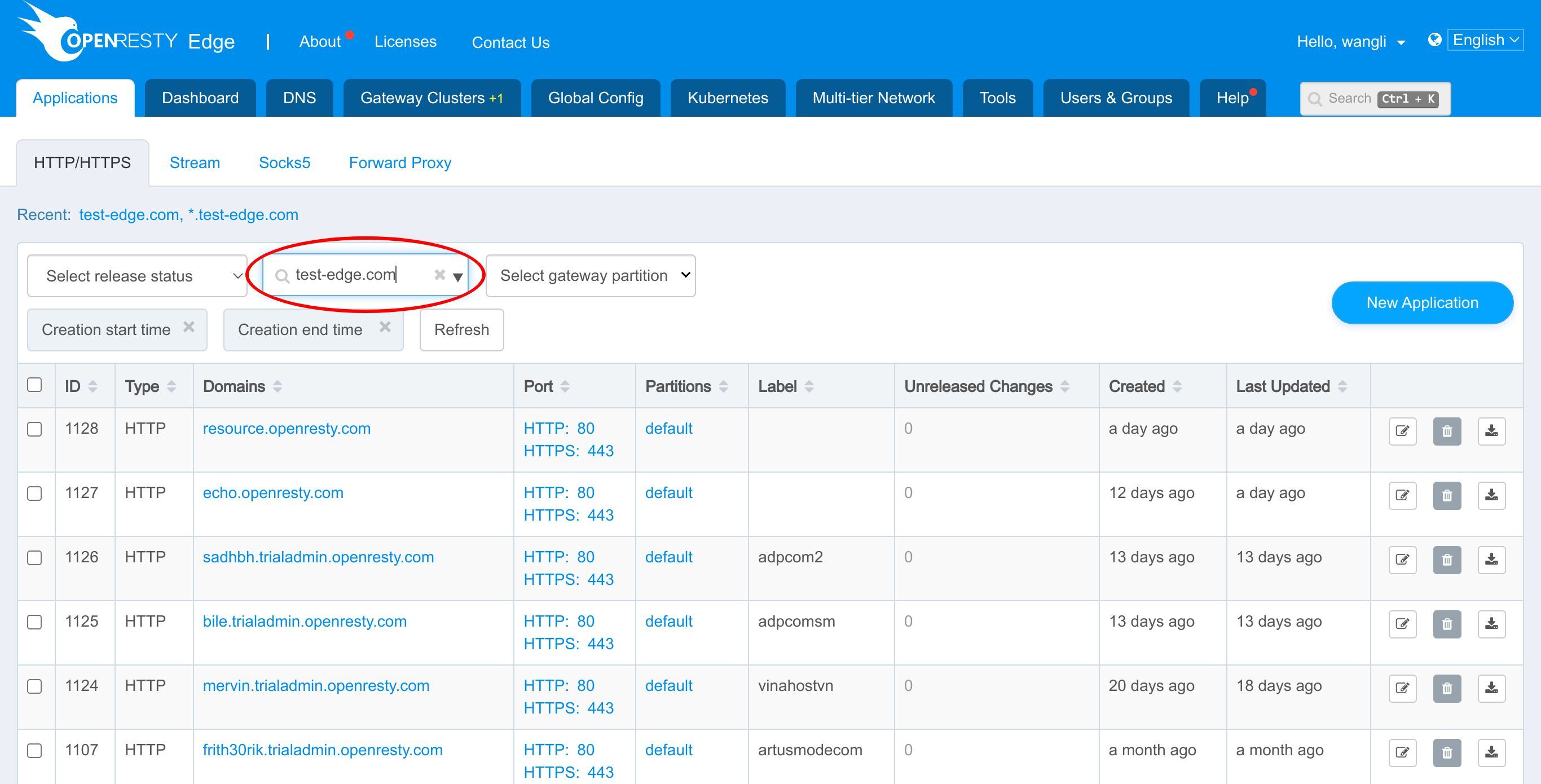
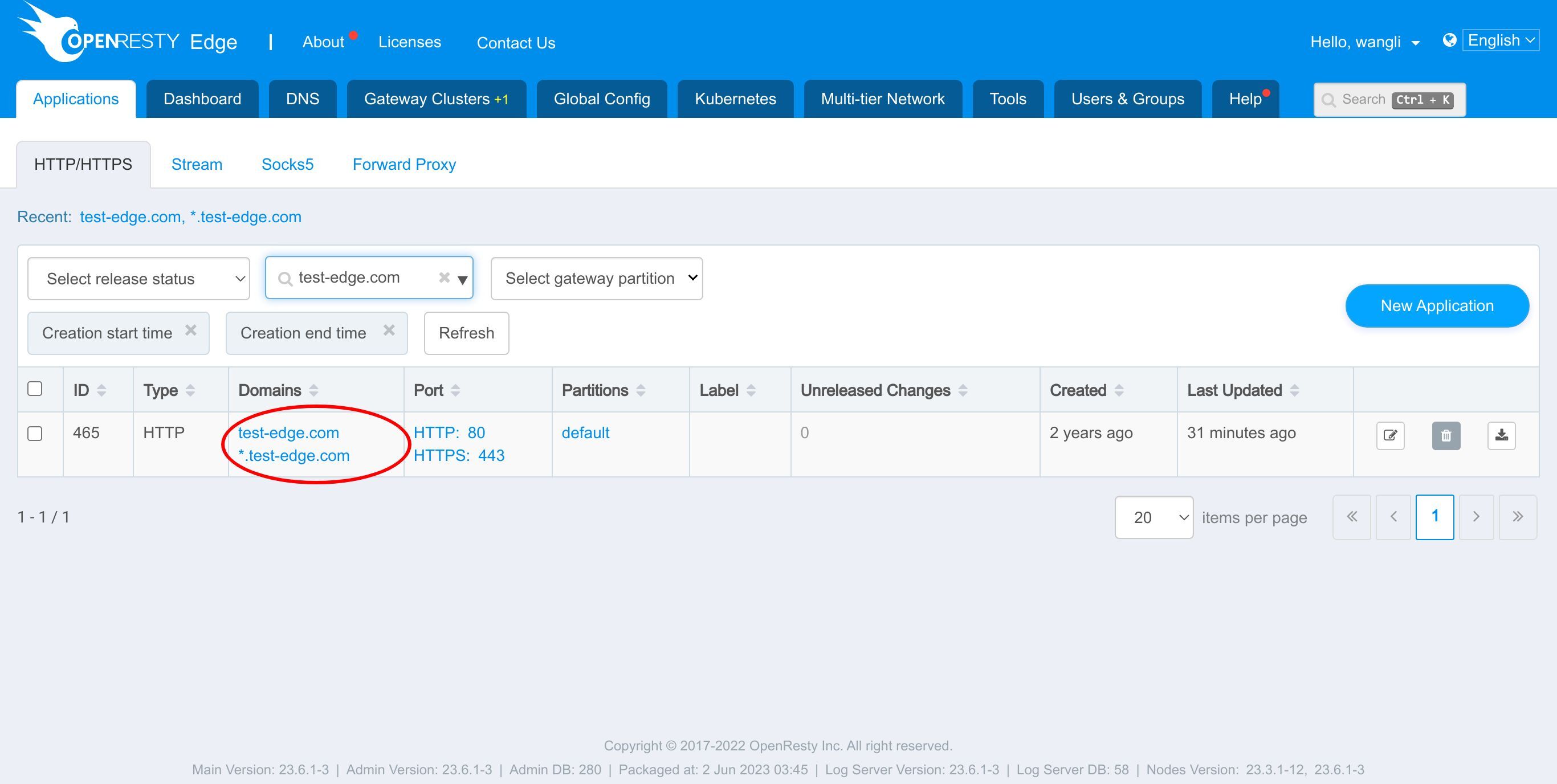
As always, let’s go to the OpenResty Edge’s Admin web console. This is our sample deployment of the console. Every user has her own local deployment.
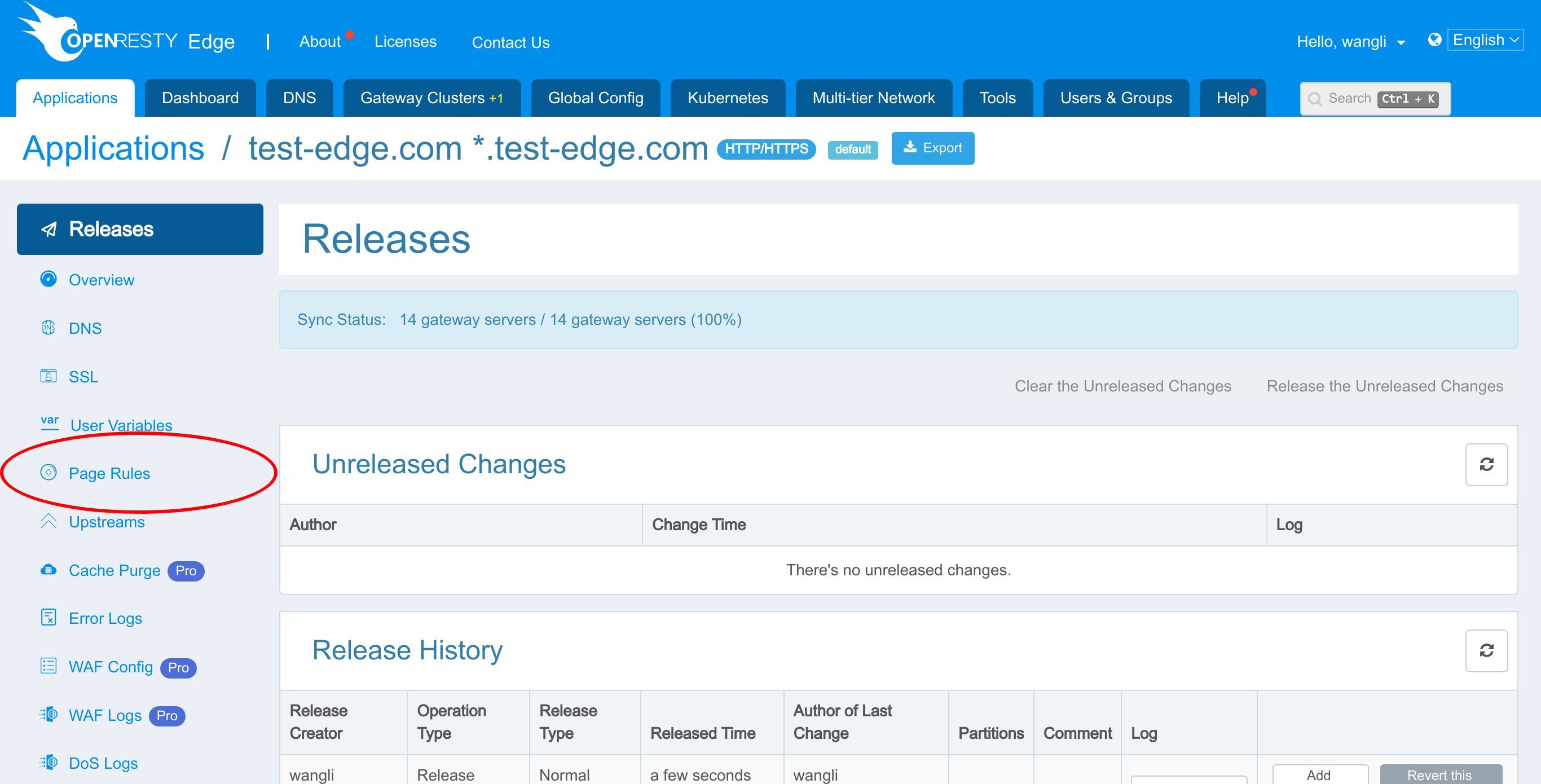
we continue with the test-edge.com domain to demonstrate OpenResty Edge’s built-in captcha.
Let’s enter this application.
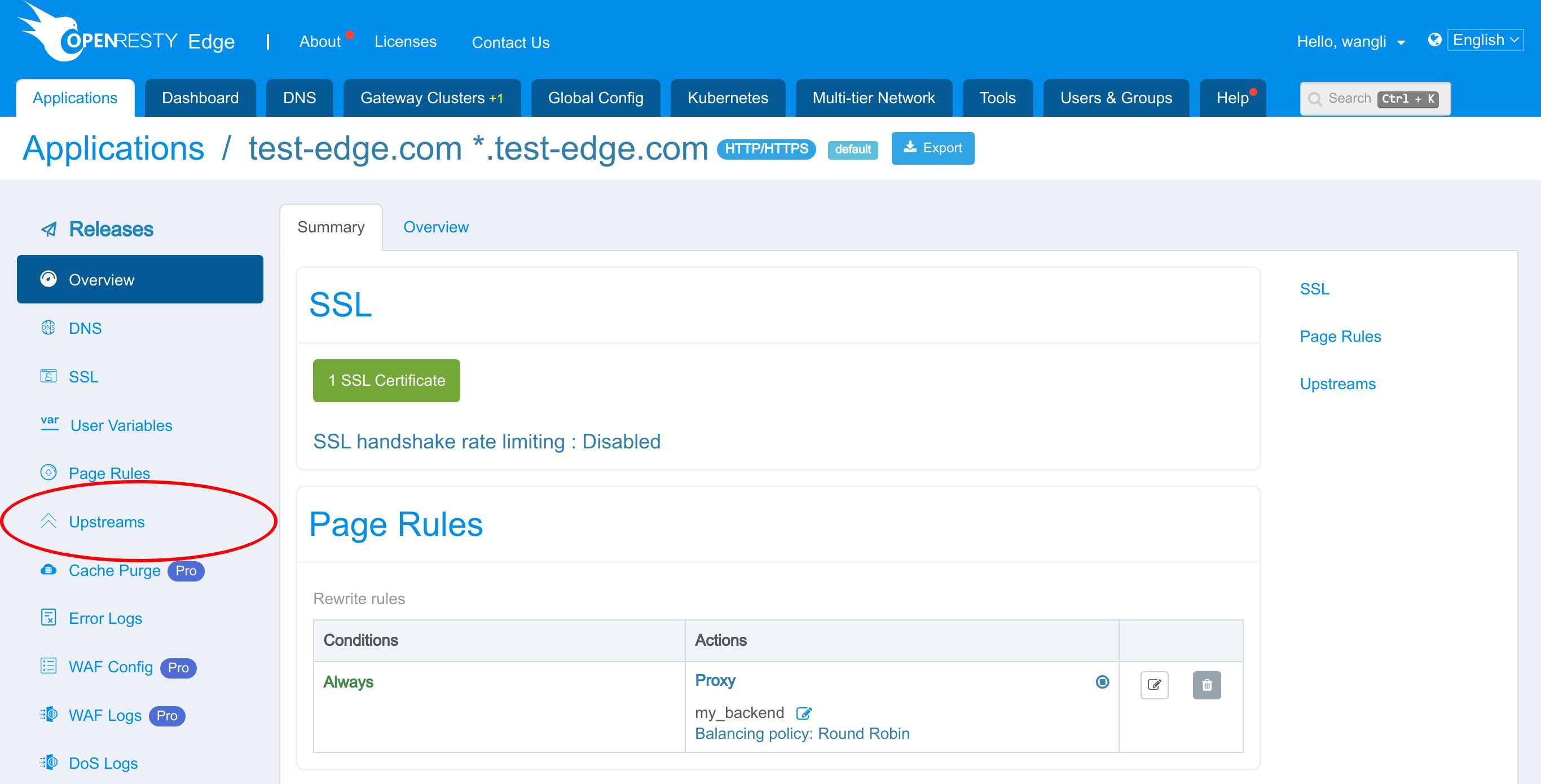
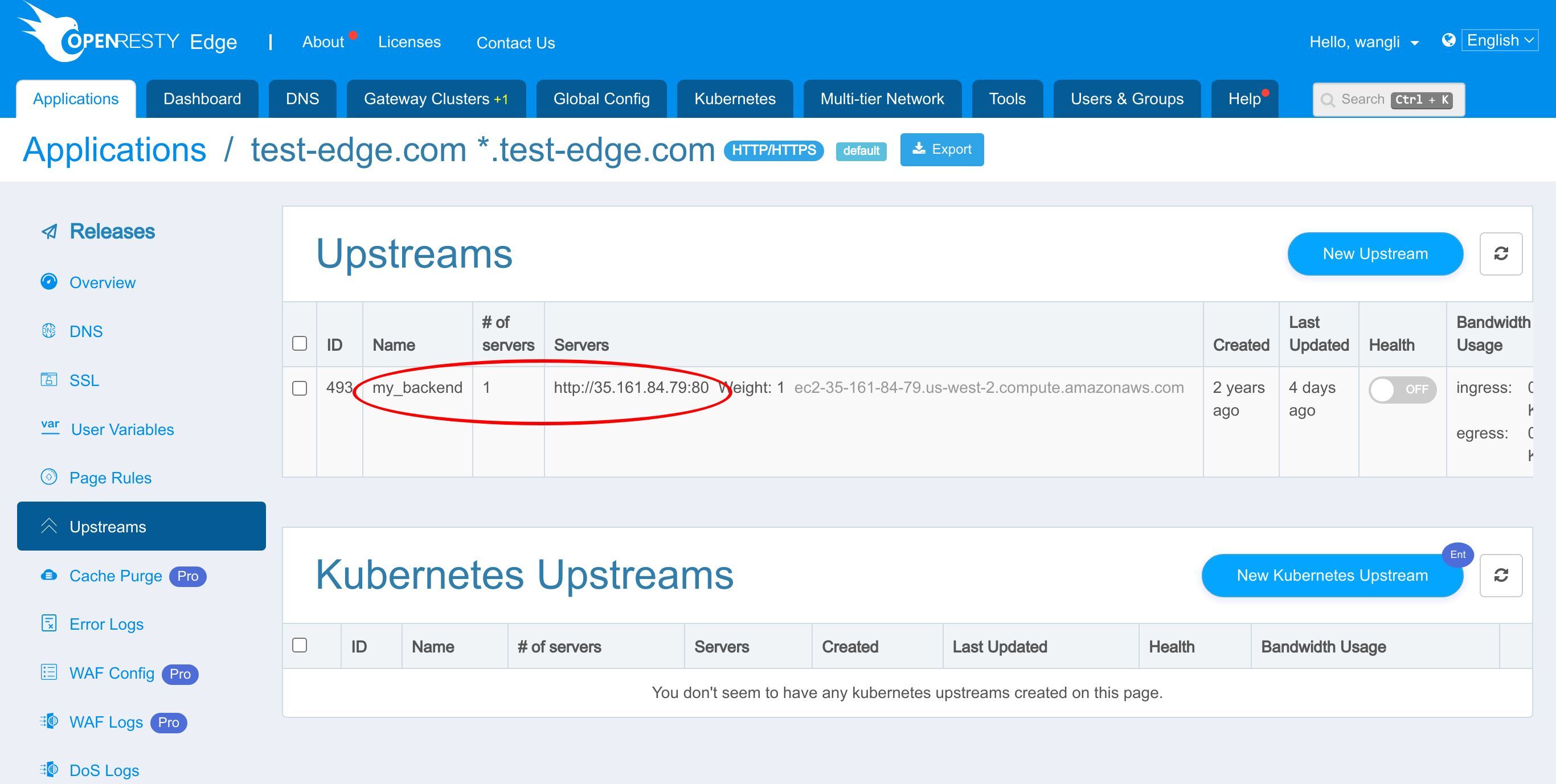
We already have an upstream defined in our earlier tutorial.
This my_backend upstream has a backend server defined already.
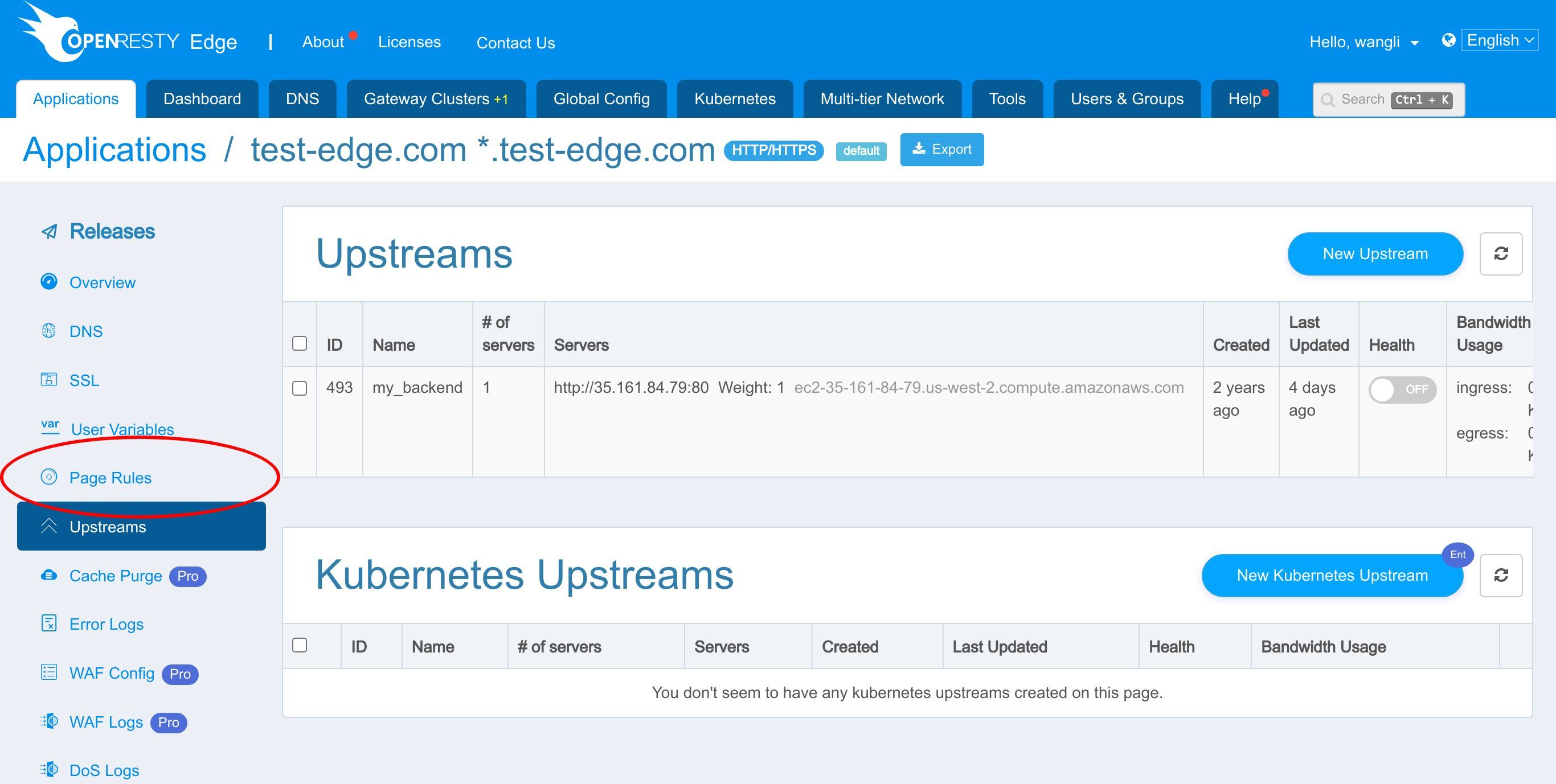
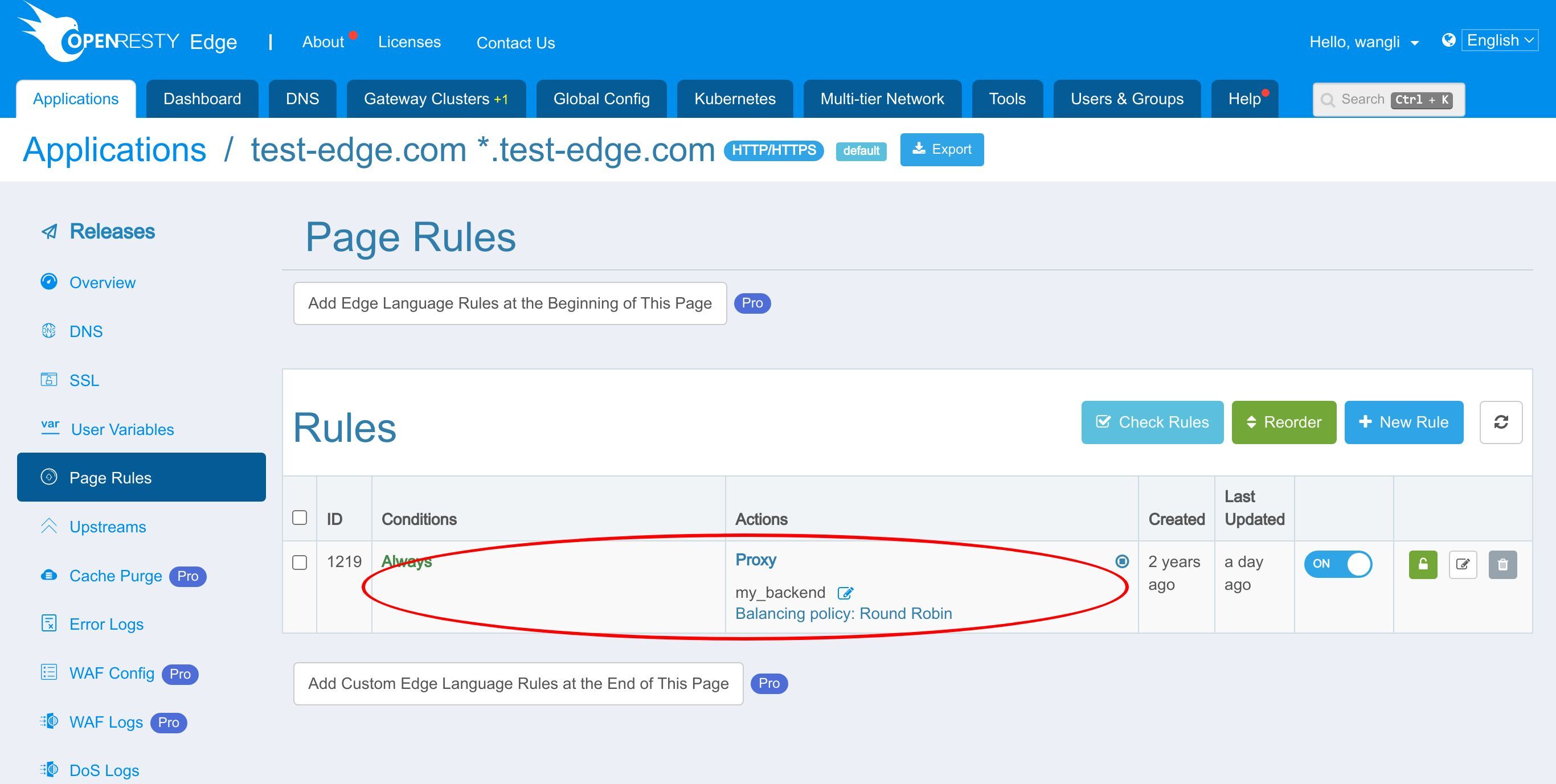
And we also have a page rule already defined.
In the previous tutorial, this page rule has set up a reverse proxy to the upstream we just saw.
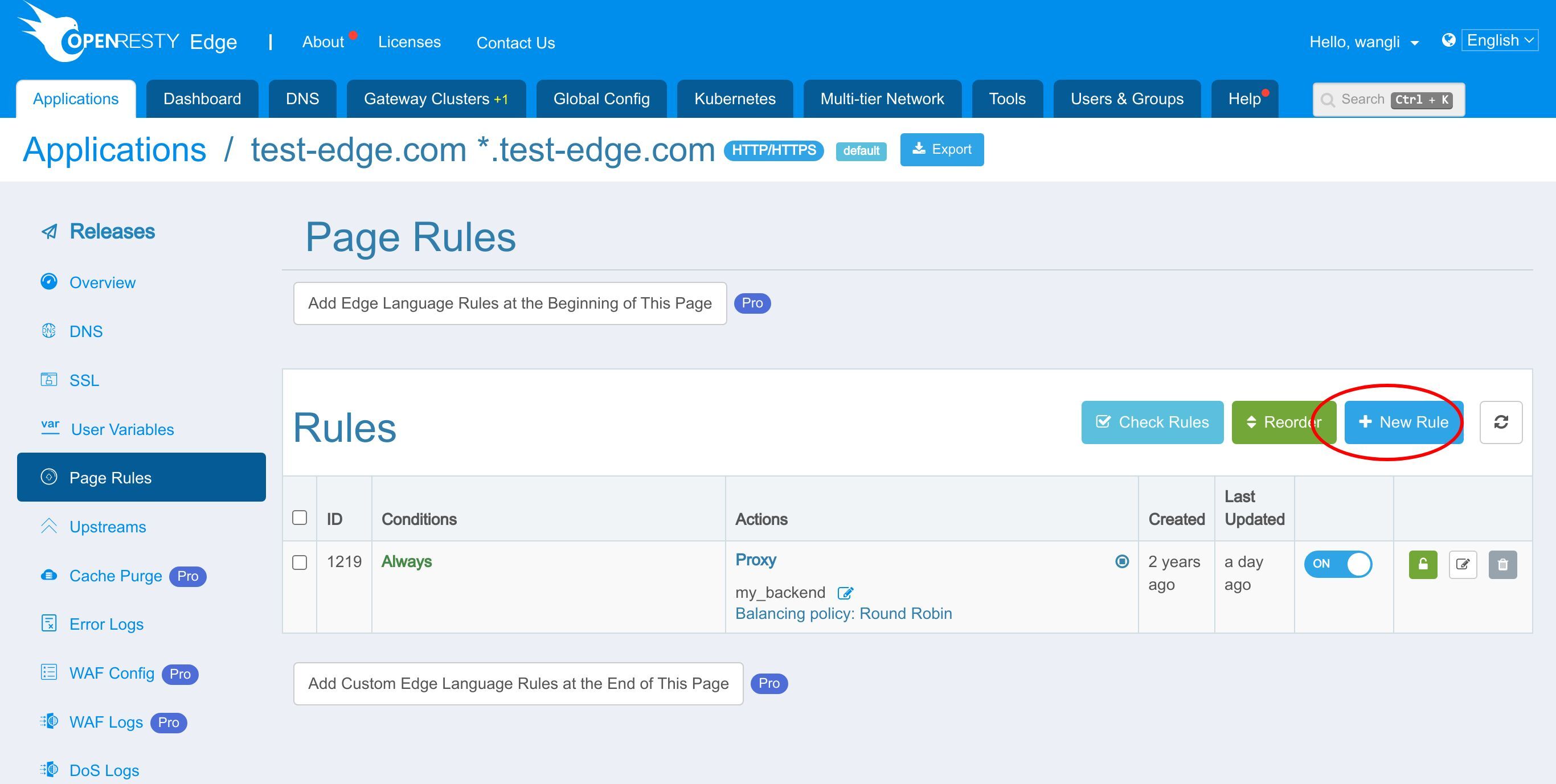
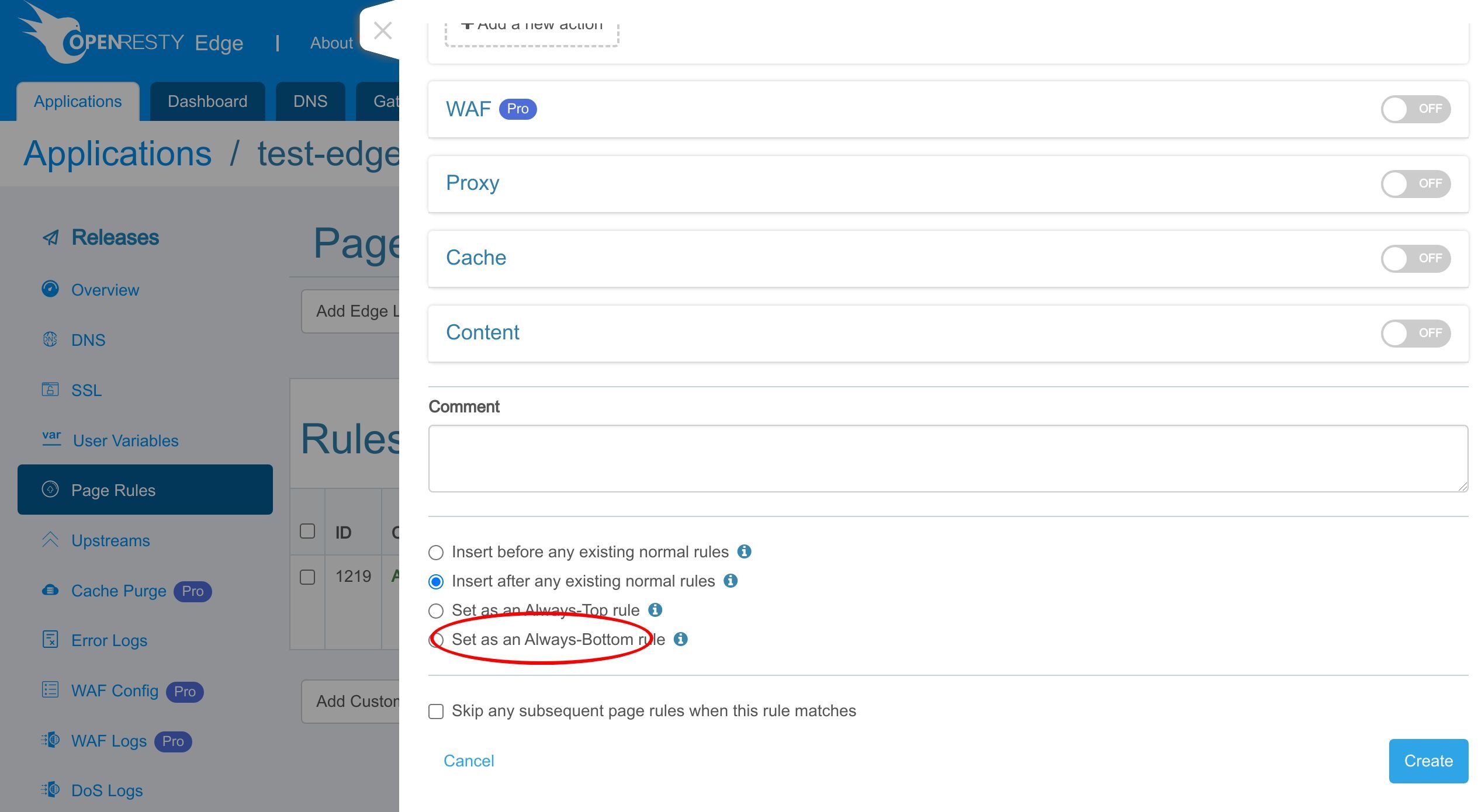
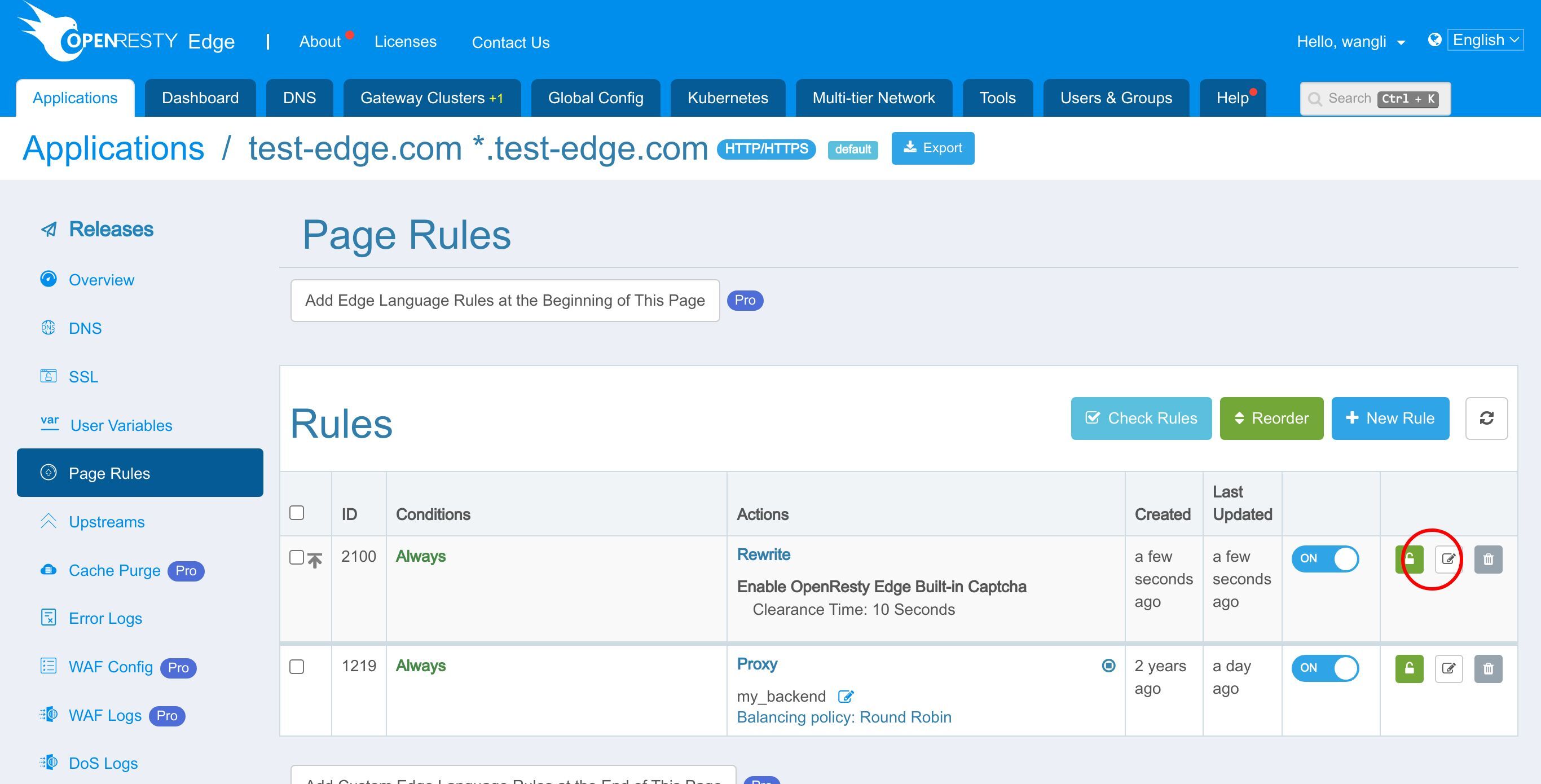
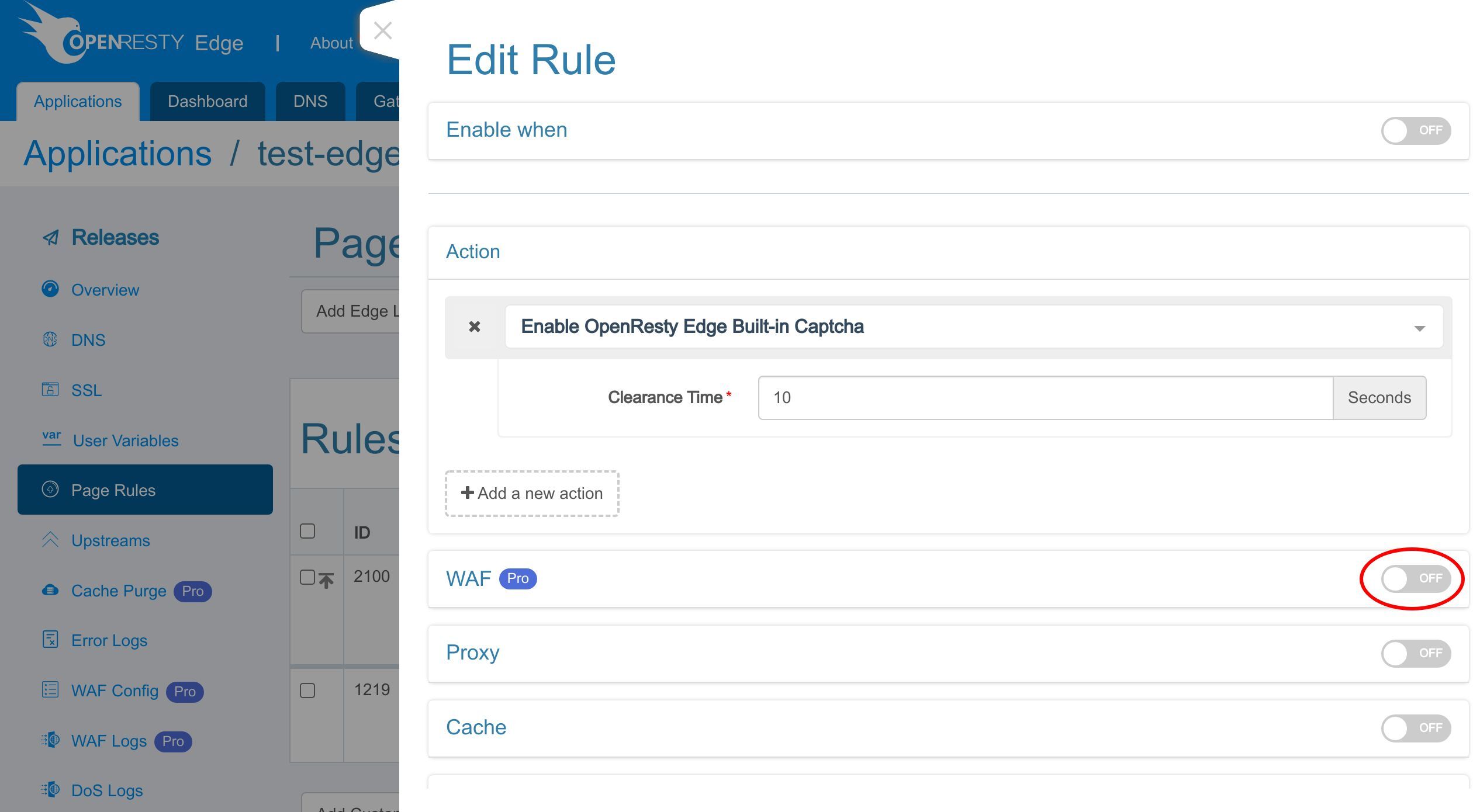
Let’s add a new page rule to enable the OpenResty Edge built-in captcha.
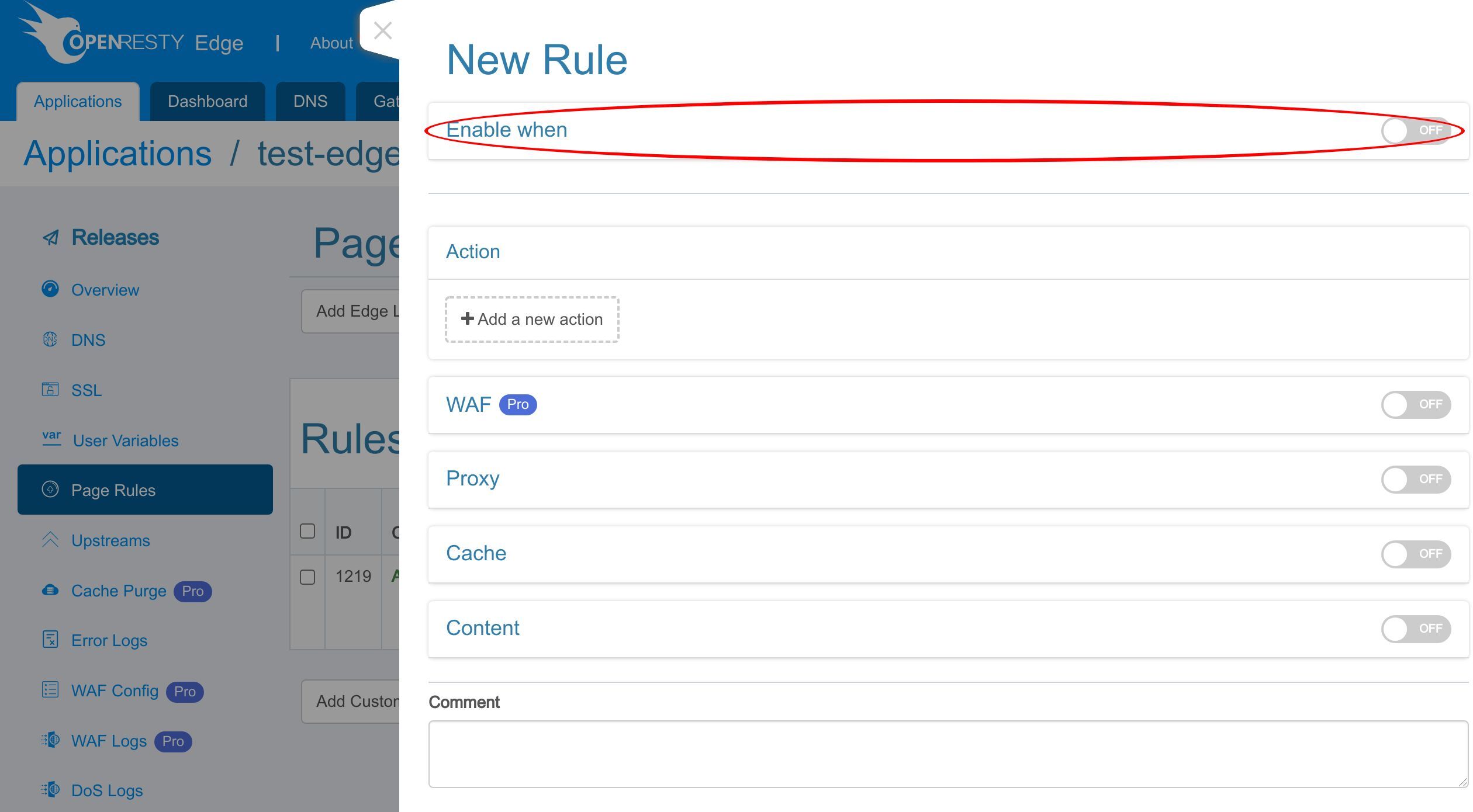
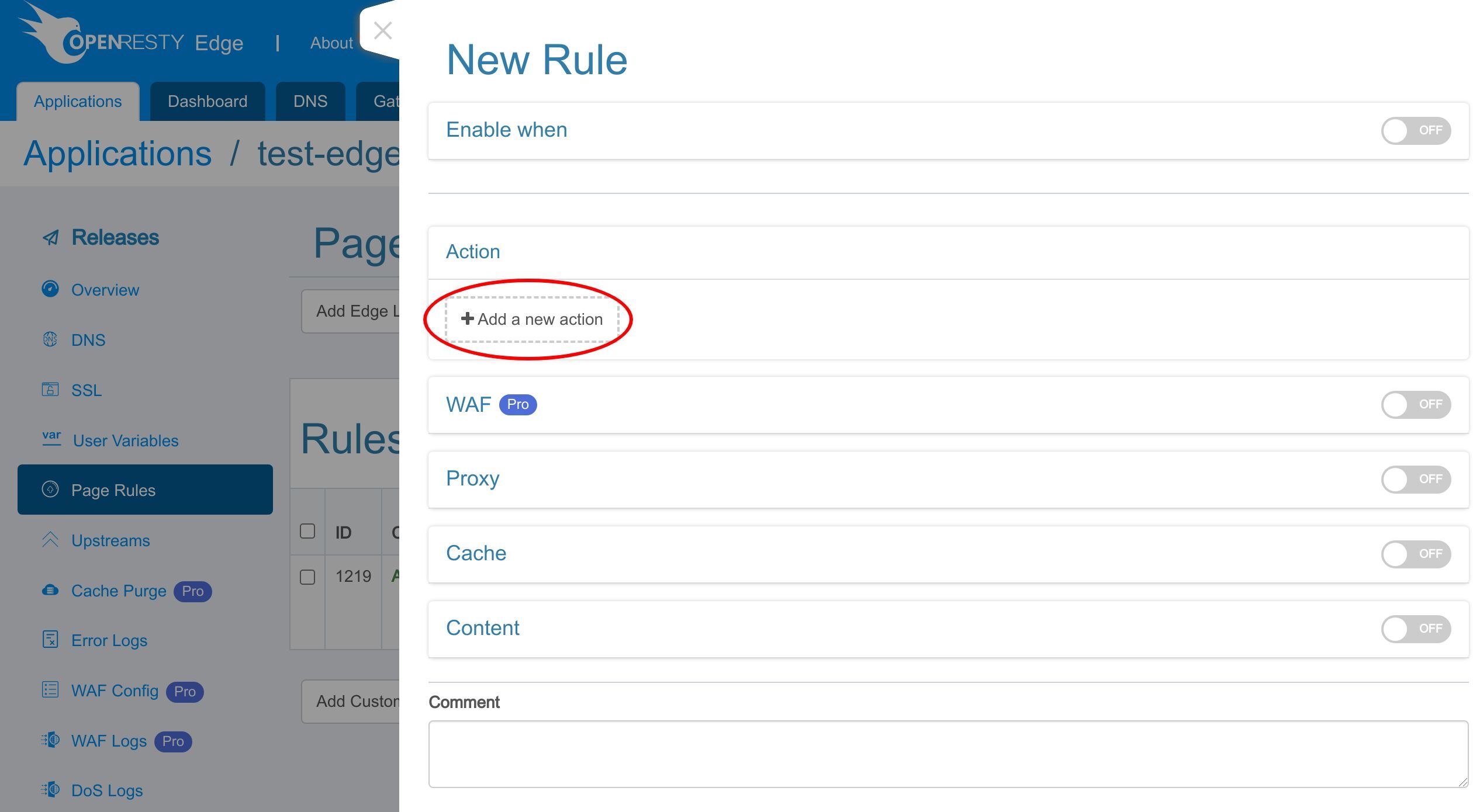
We do not specify a condition for this rule. So it will fire unconditionally.
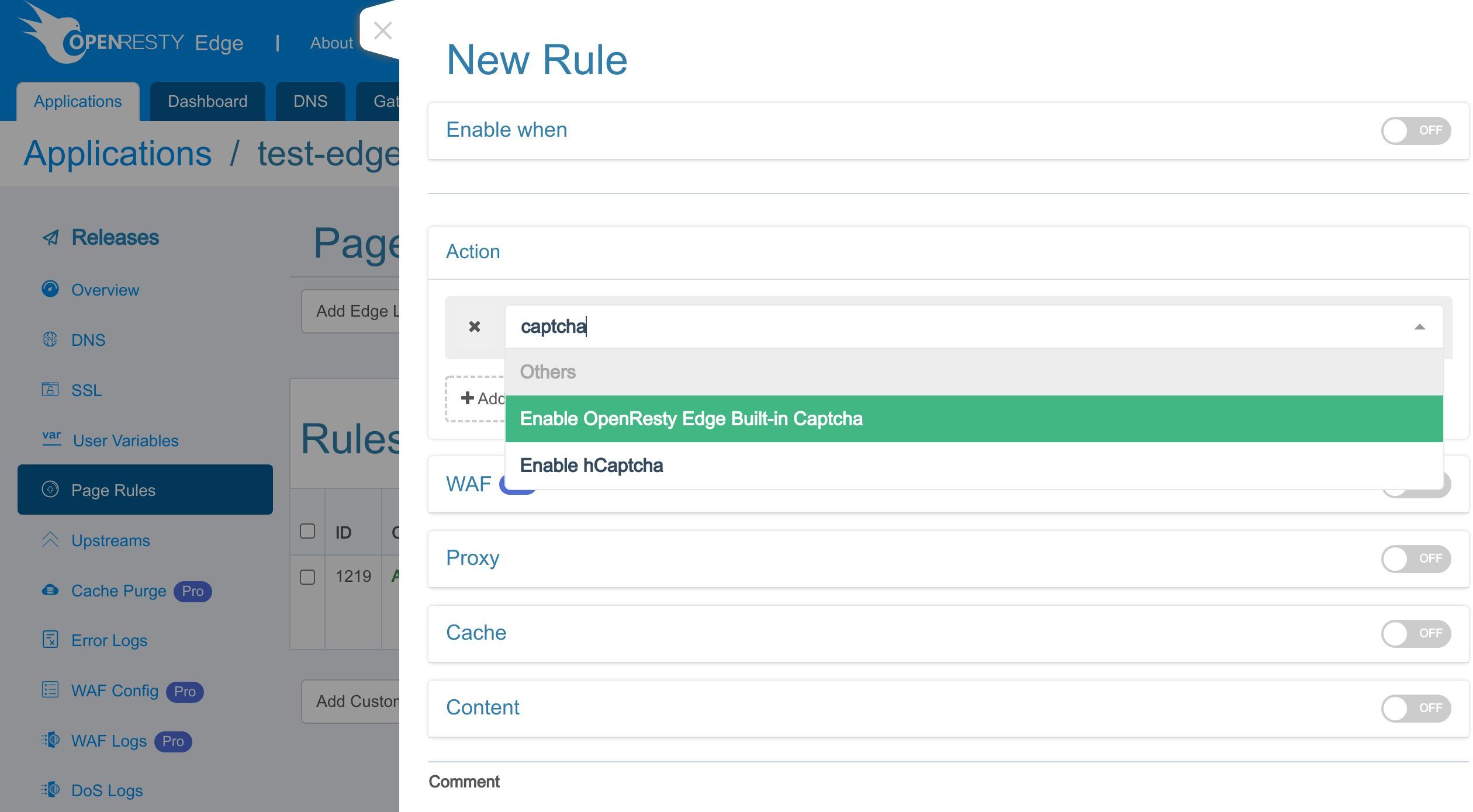
Let’s add a new action.
Type “captcha” for search.
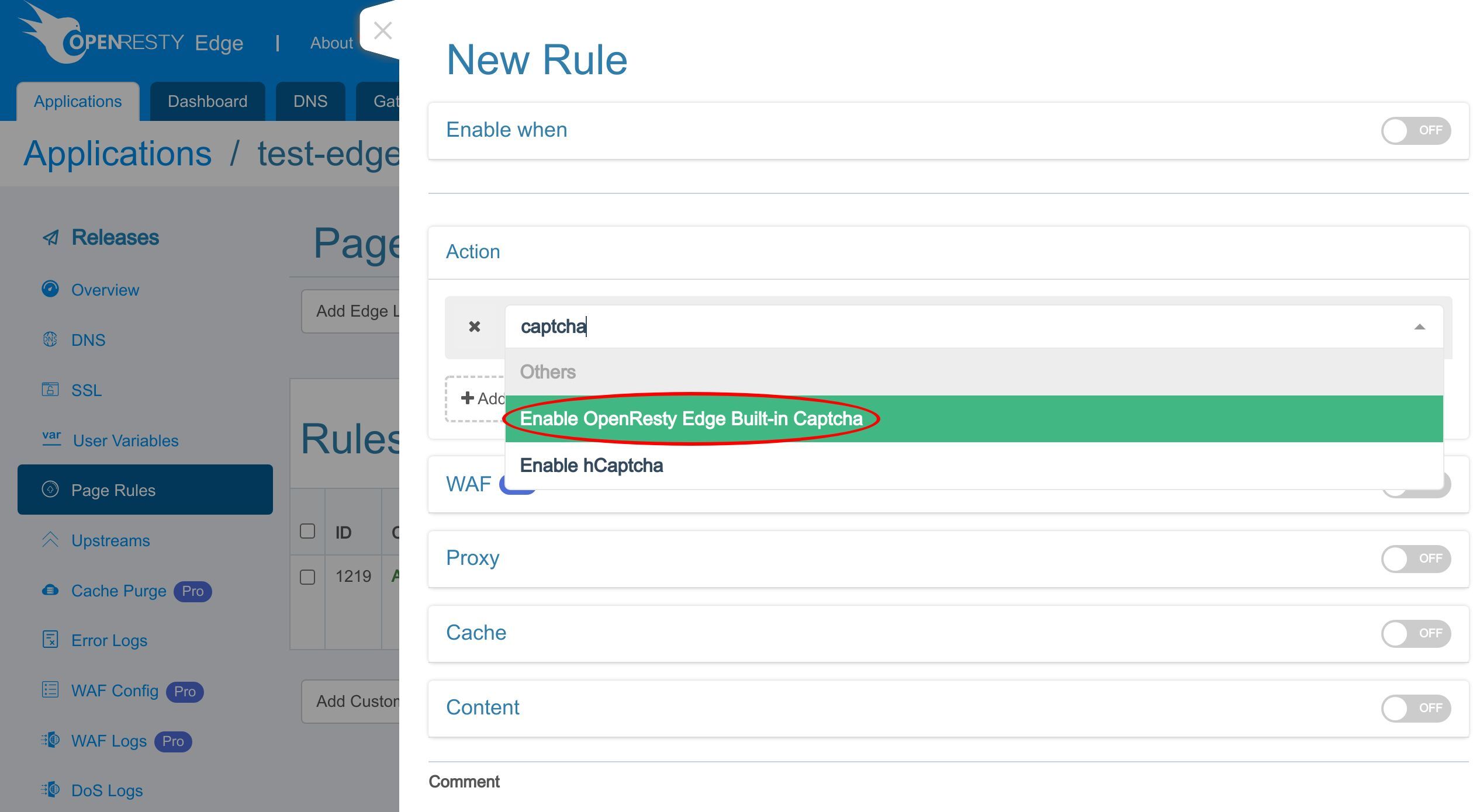
Select the option “Enable OpenResty Edge Built-in Captcha”.
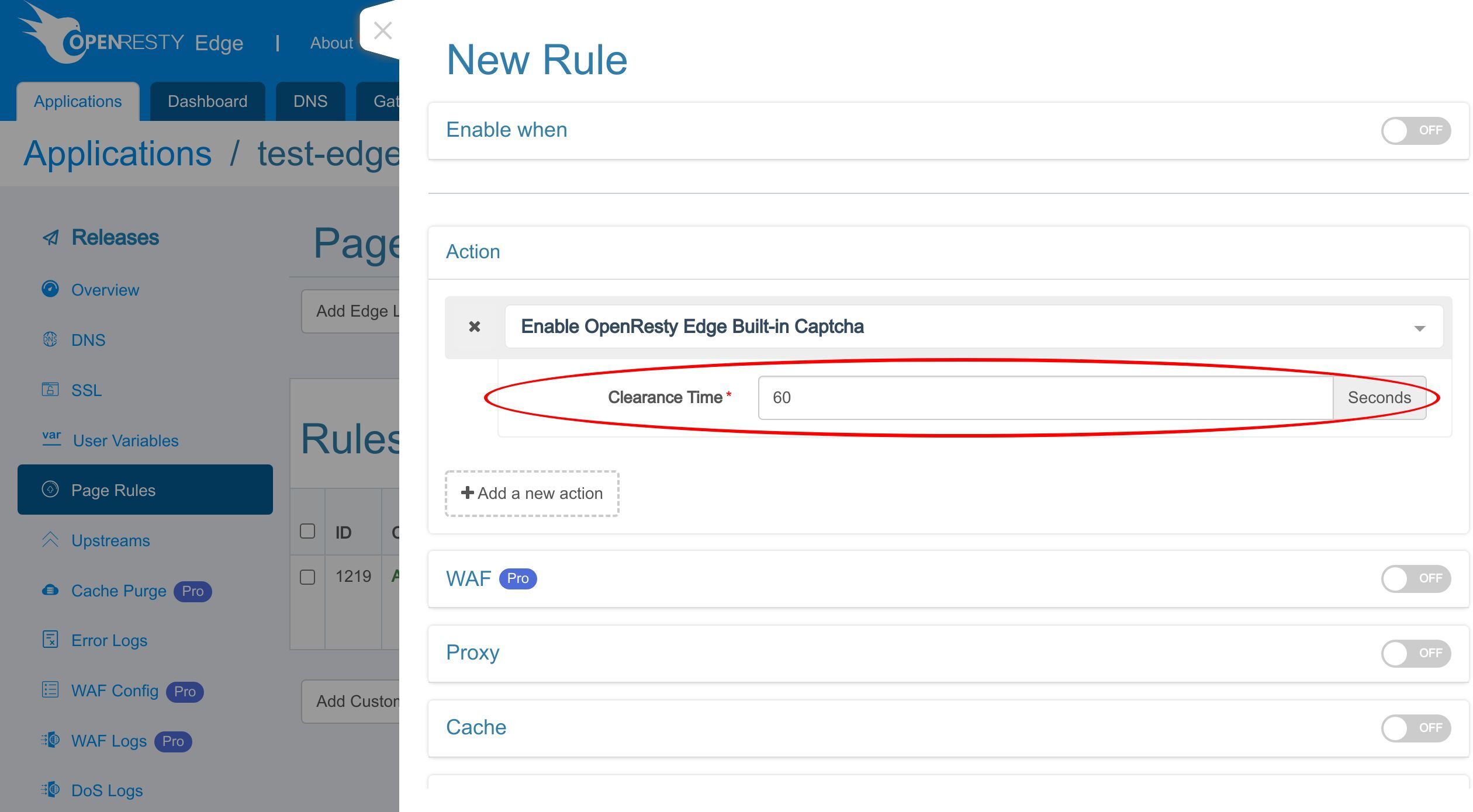
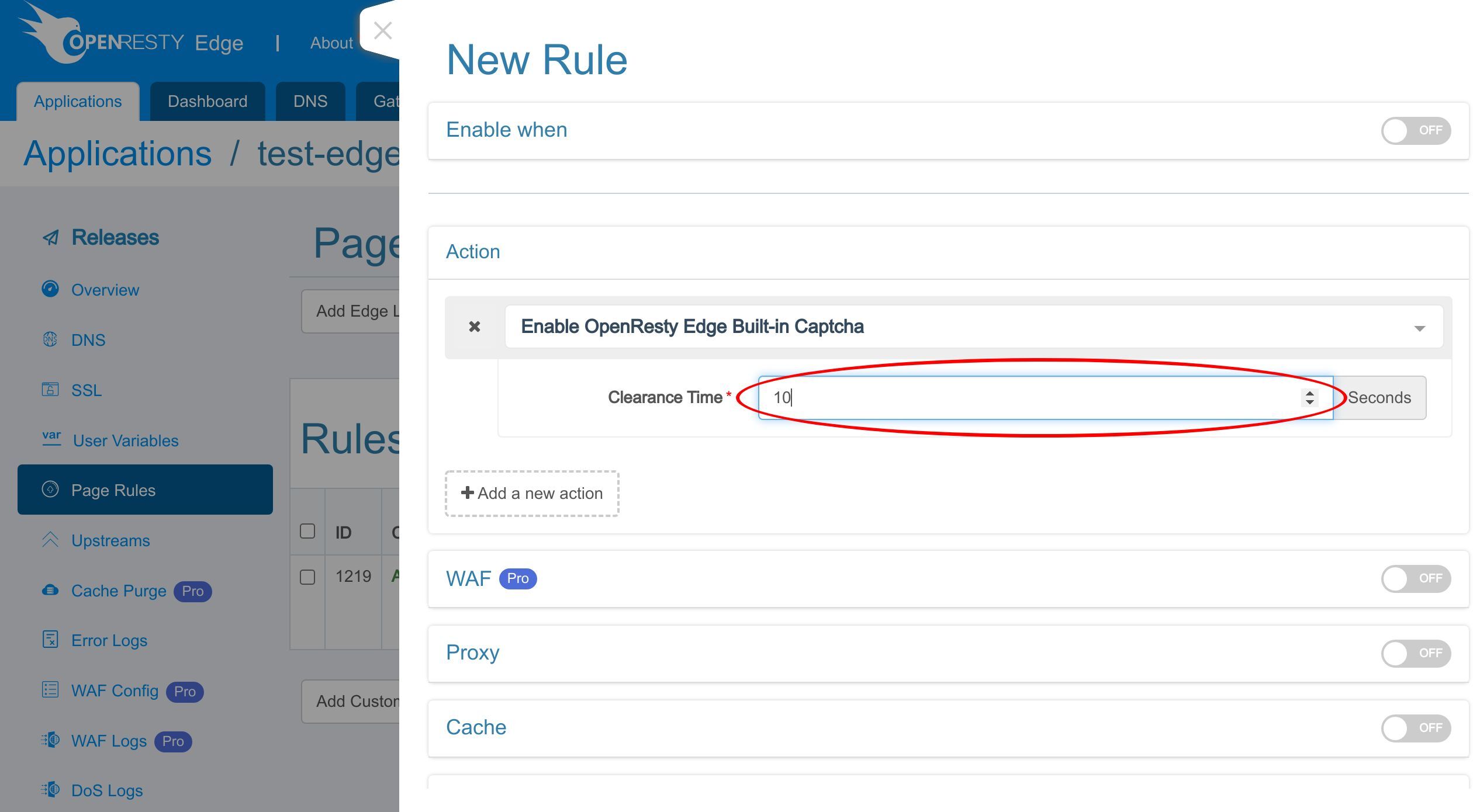
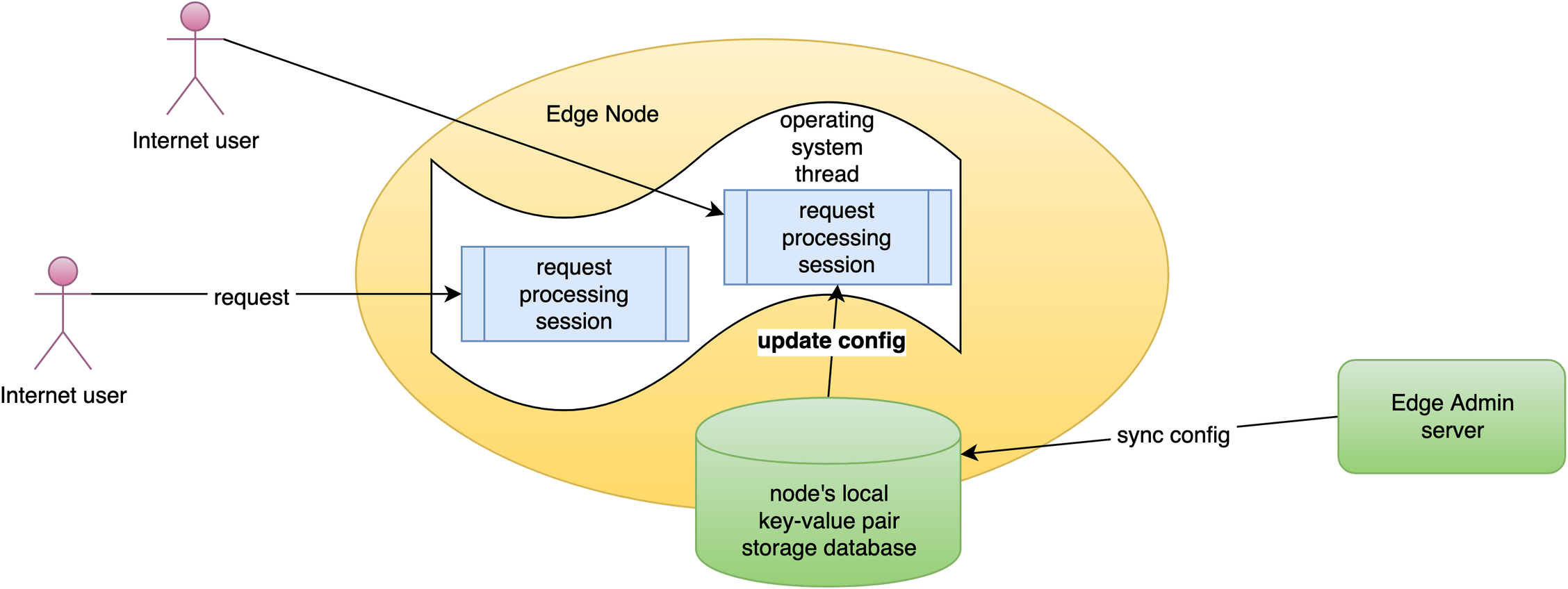
Clearance time means that when the client passes the captcha verification, the OpenResty Edge will allow all requests from the same client in the specified period. Captcha records the verification information through cookies.
We set the time to 10 seconds.
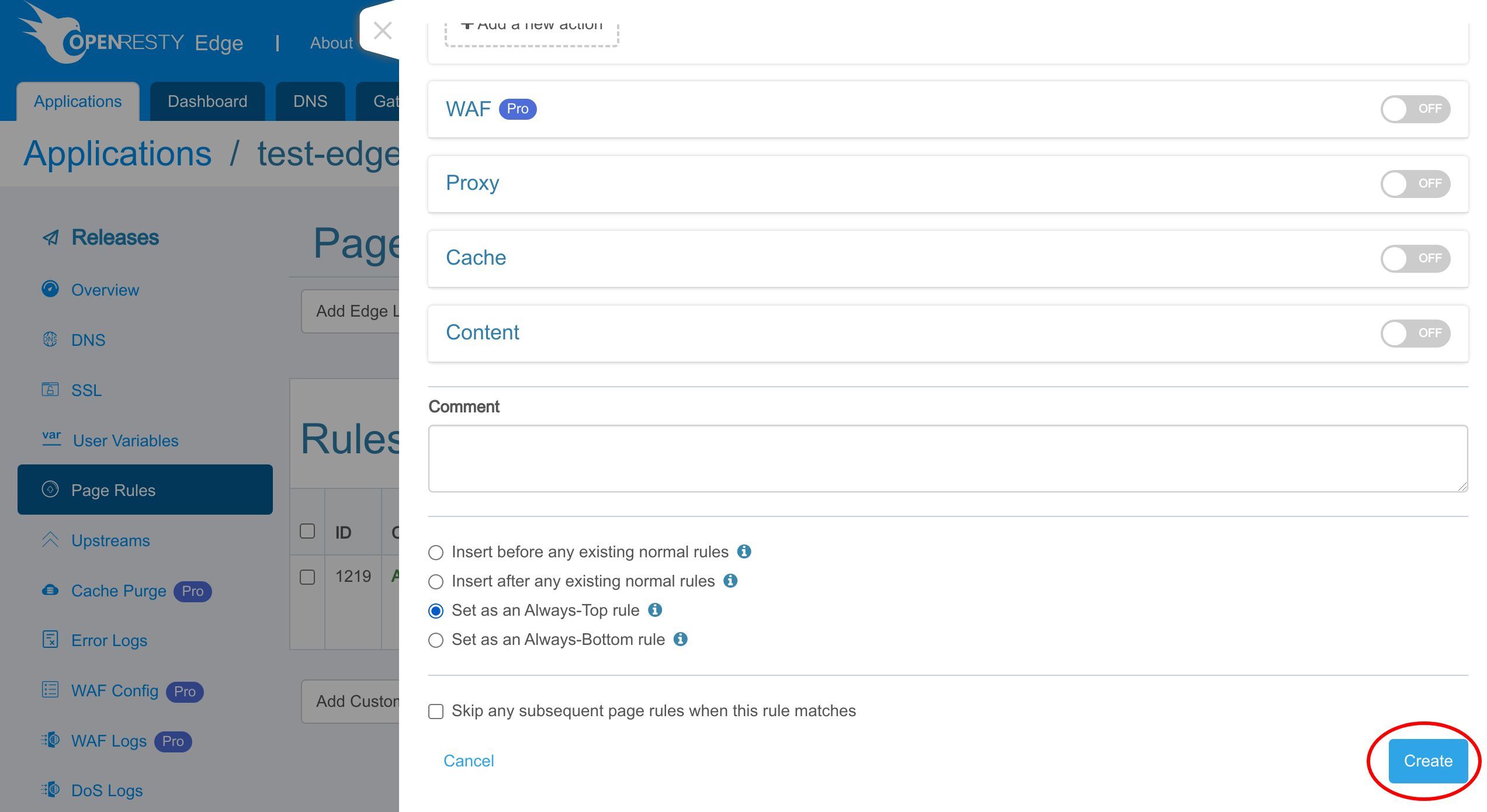
We insert this rule as an always top rule to ensure this rule is executed first. This is for our demonstration. You can set any order you want.
Save this rule.
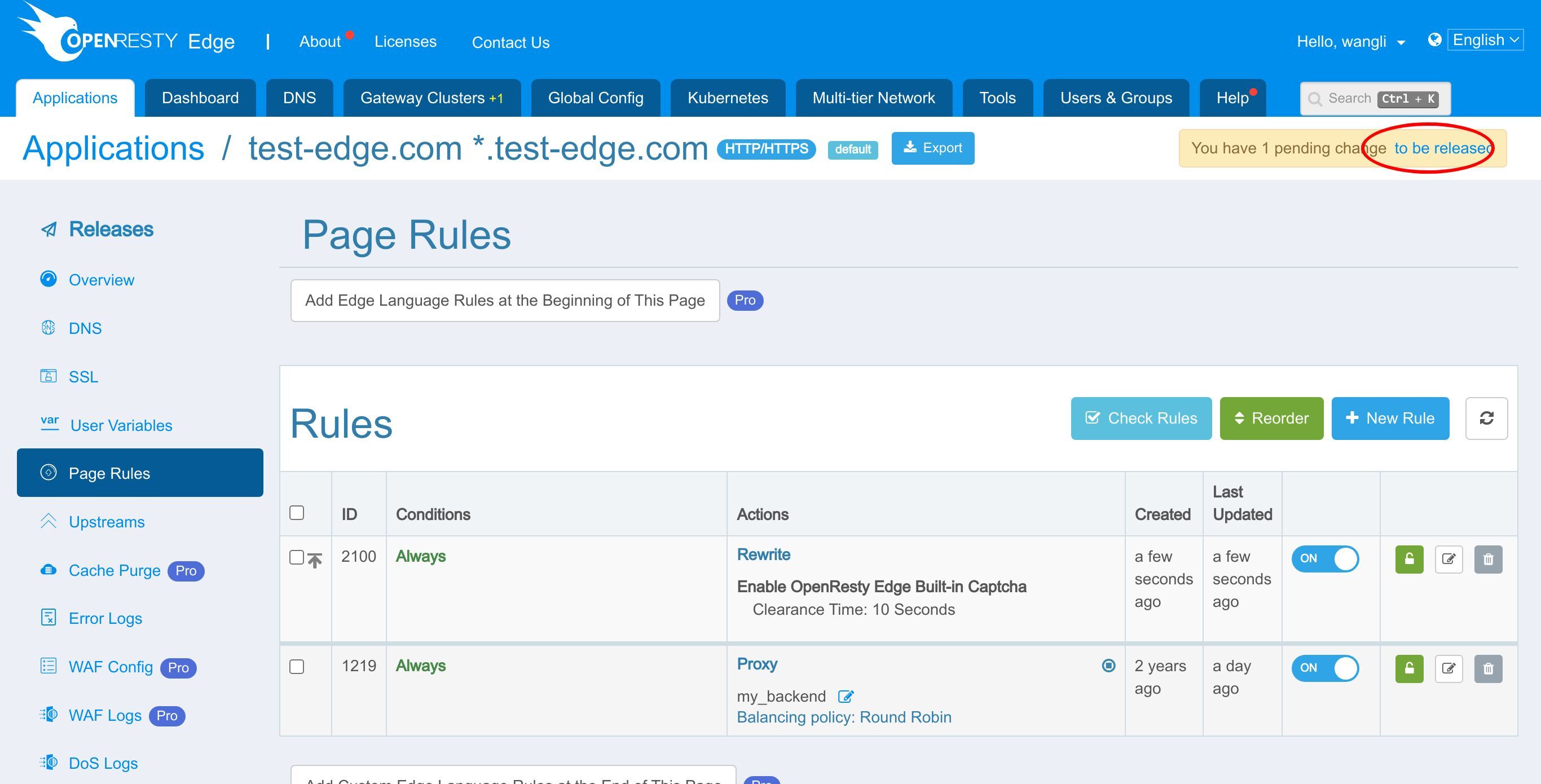
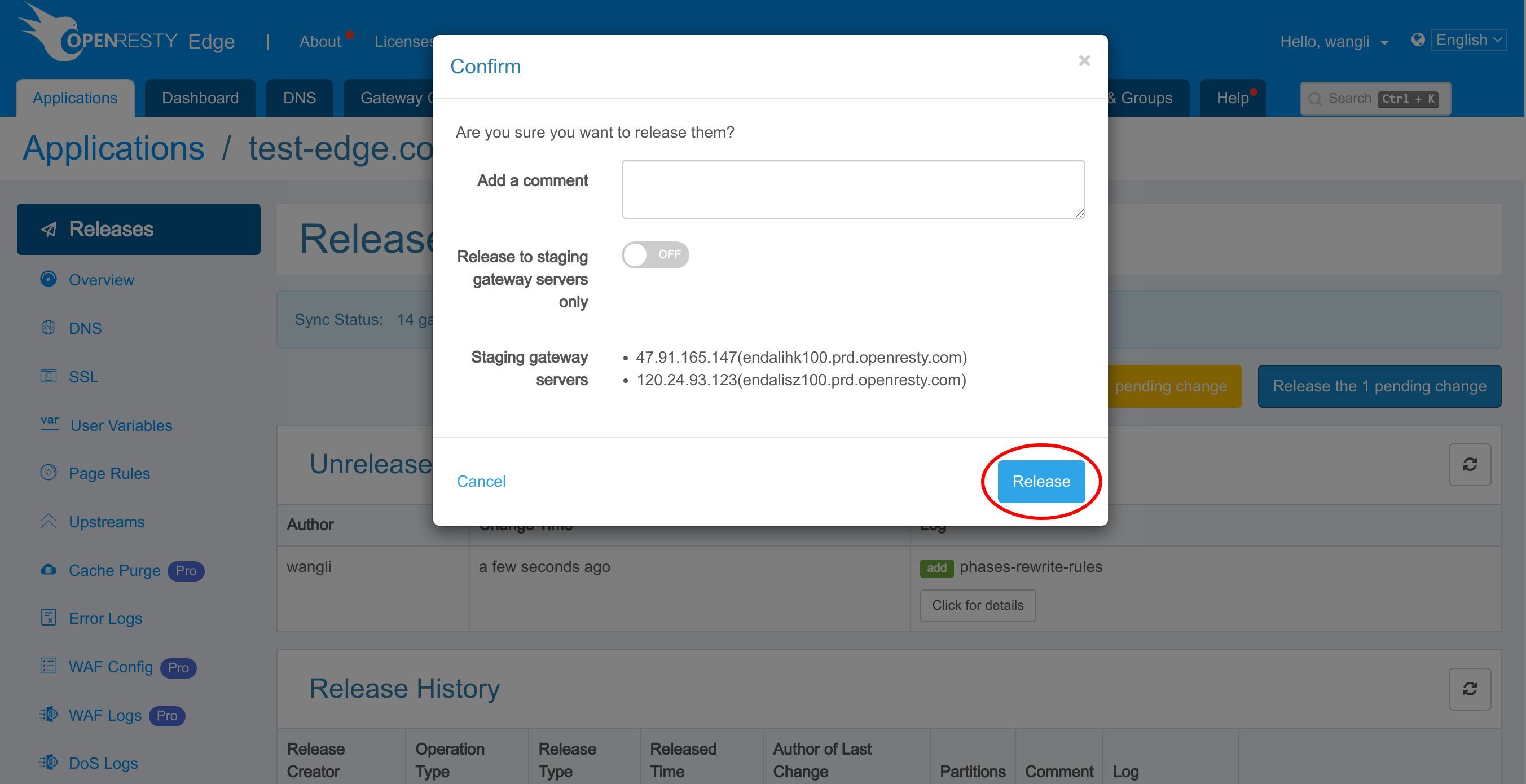
As always, we need to make a new release to push out our edited page rule.
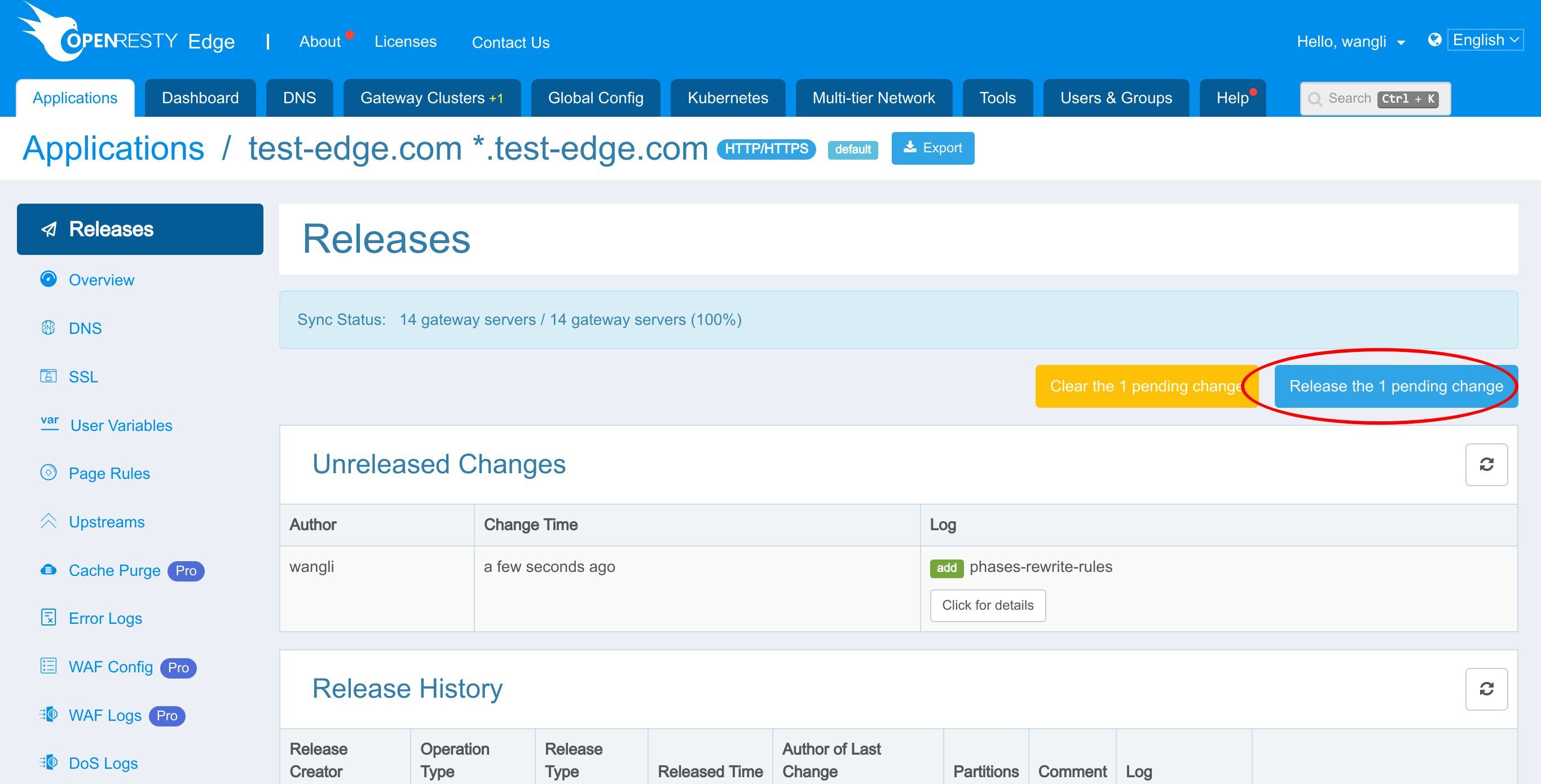
Click on this button.
Ship it!
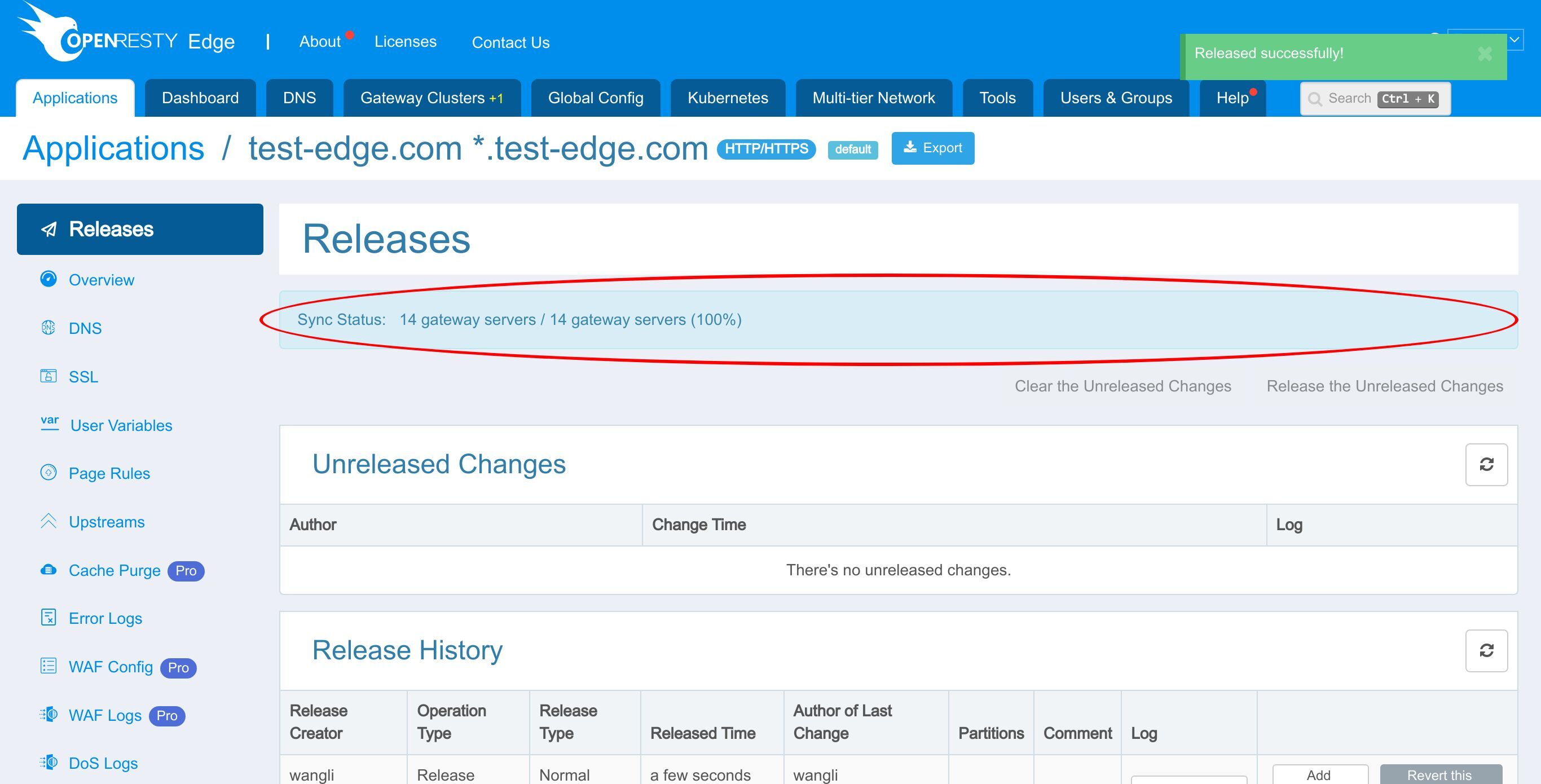
It is fully synchronized.
Now the new page rule has been pushed to all the gateway clusters and servers.
Our configuration changes do NOT require server reload, restart, or binary upgrade. So it’s very efficient and scalable.
Test
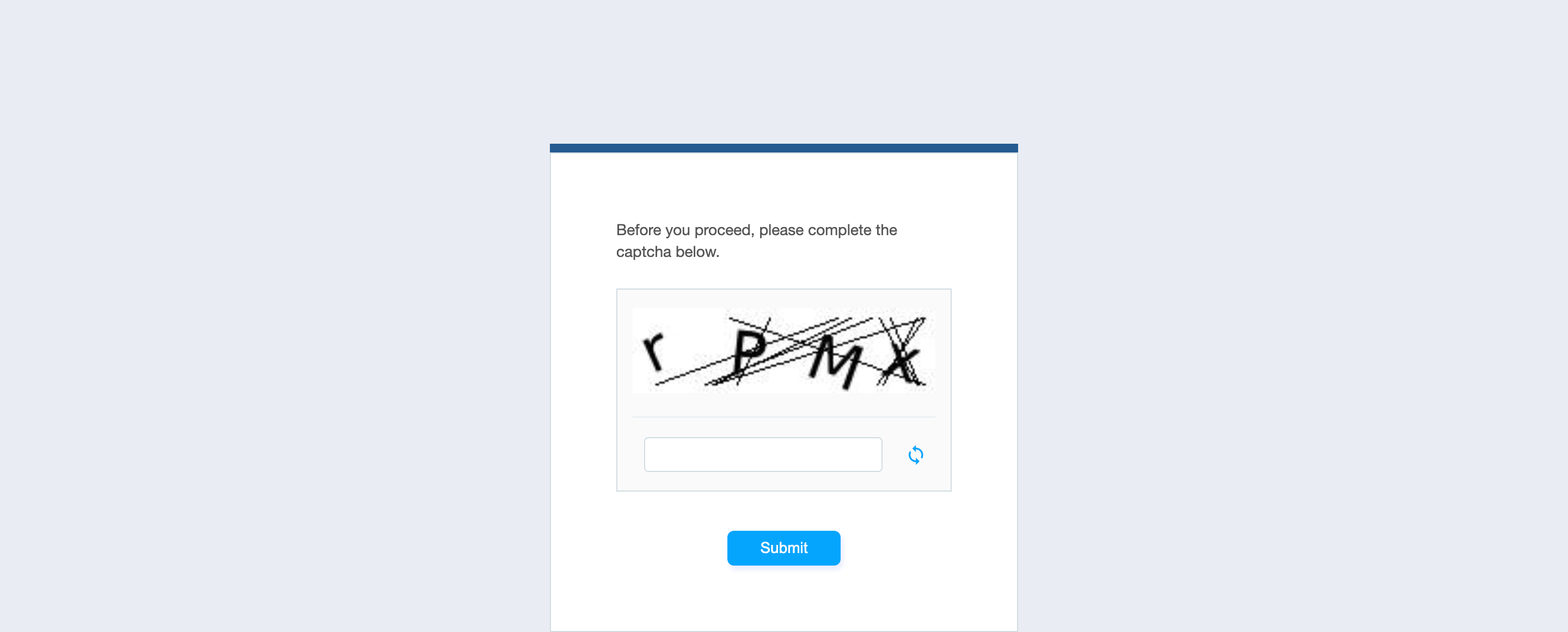
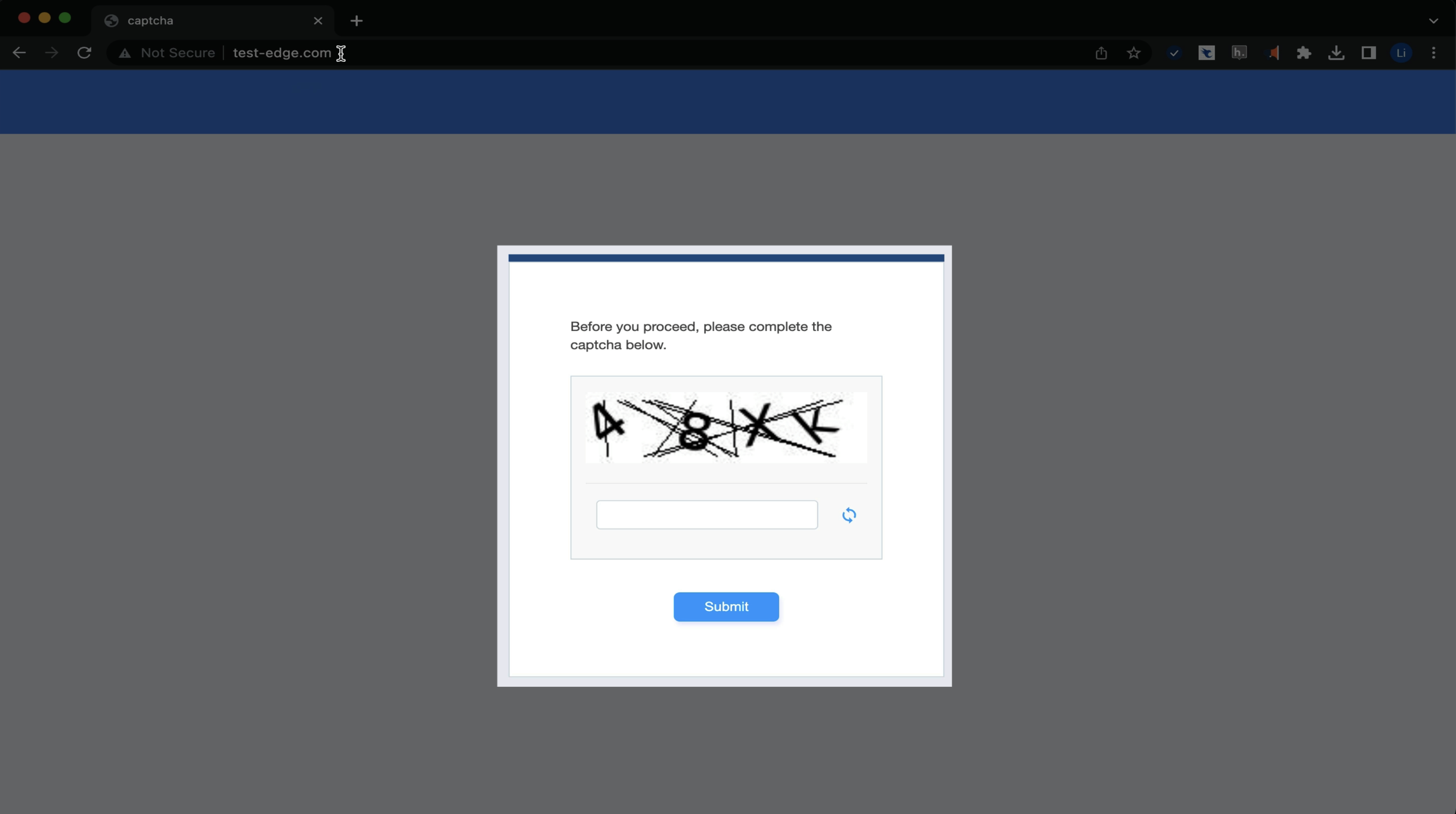
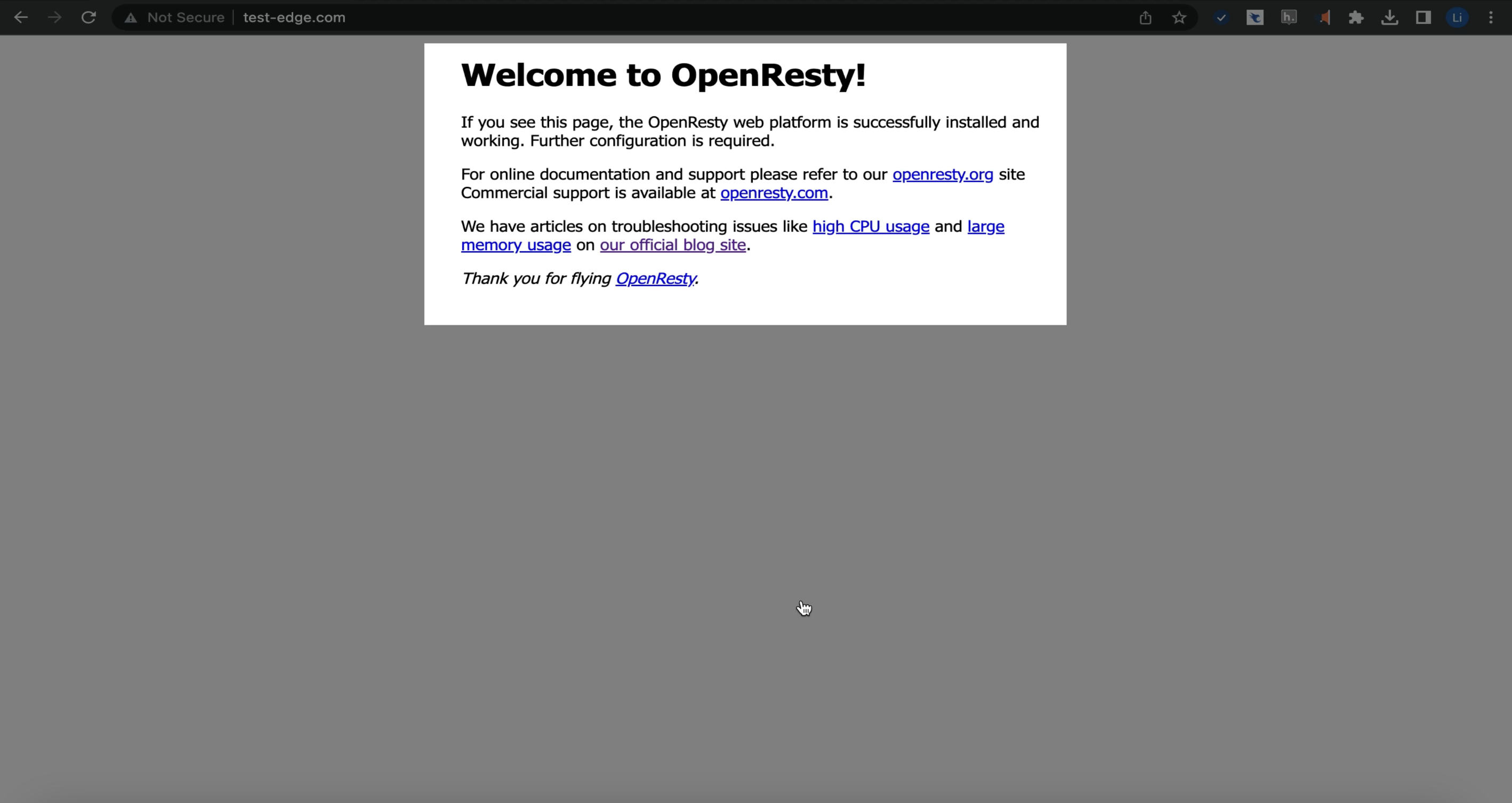
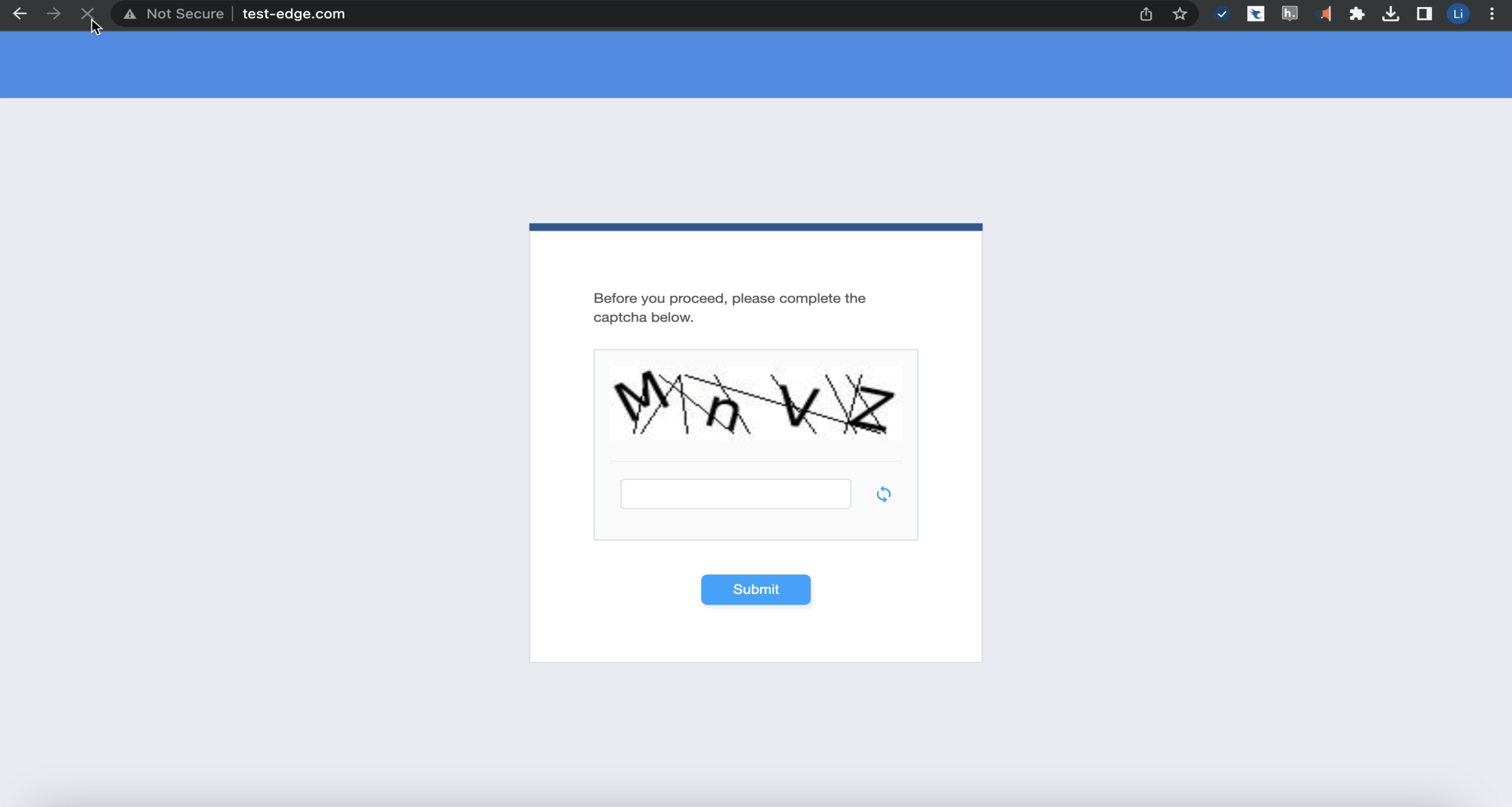
Now let’s access the application. We can see that the page returns the OpenResty Edge built-in captcha page instead of our original content.
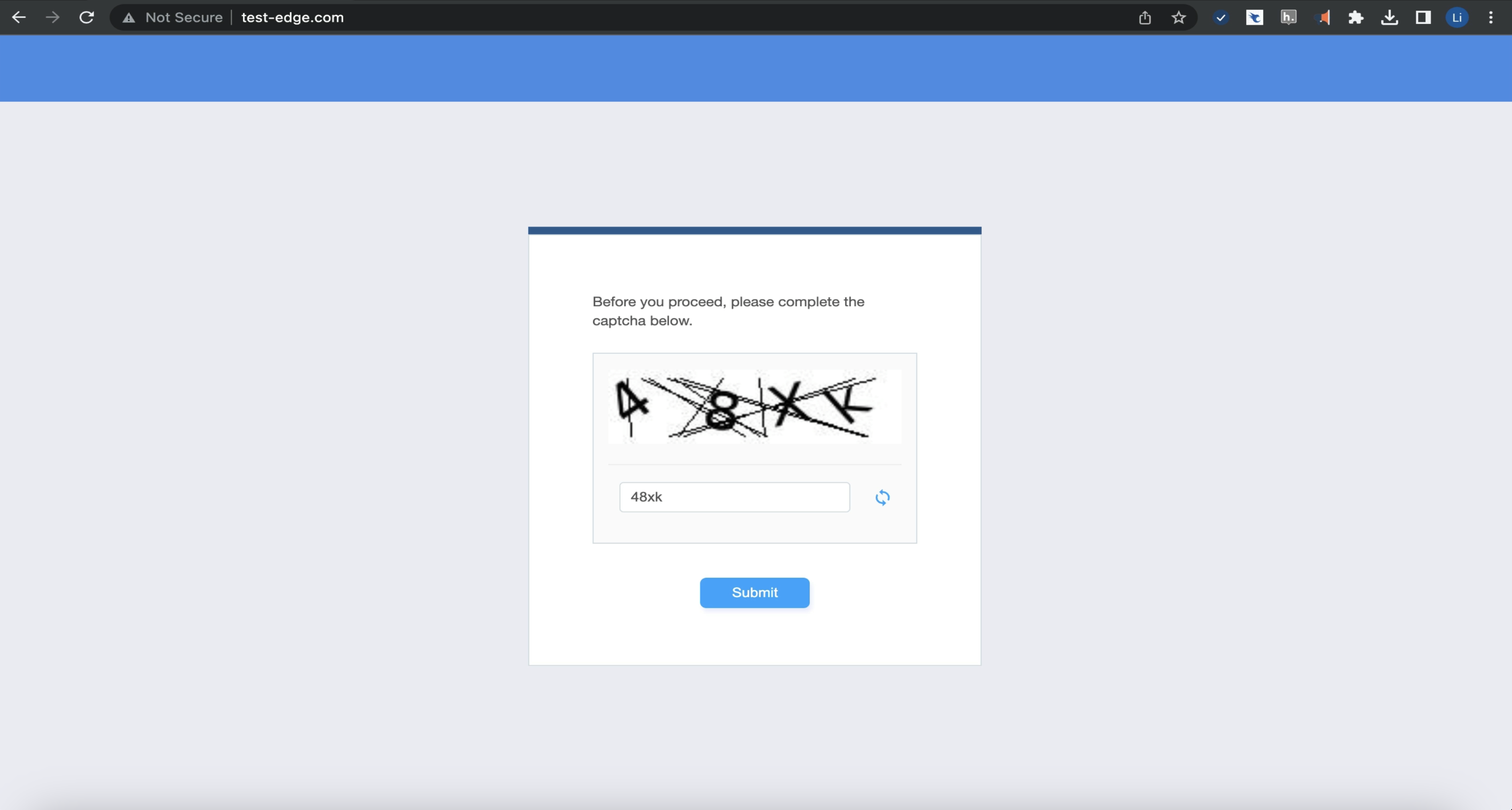
Let’s enter the captcha code.
We can see the expected content of the URI. Remember we just set the clearance time to 10 seconds. We can access the application without captchas within 10 seconds.
After 10 seconds, we need to verify again.
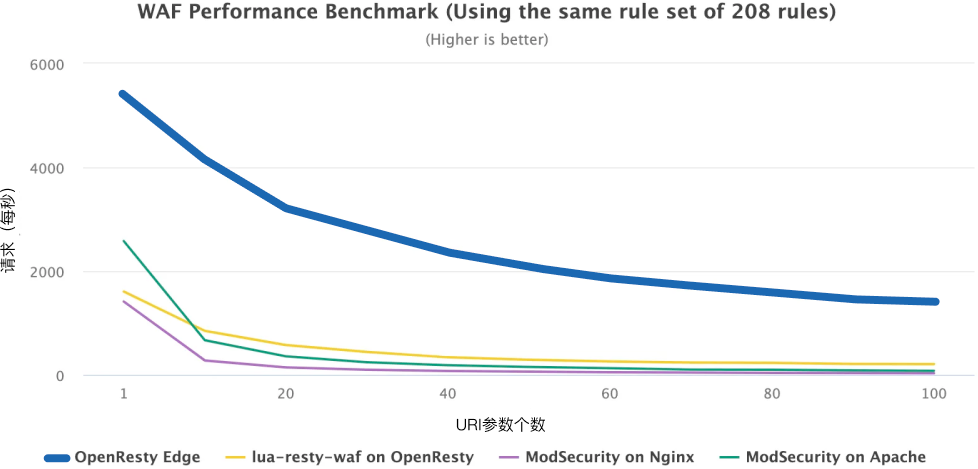
In addition to setting the captcha in the action, we can also set it in the WAF rules. We will subsequently explain the specific features of the WAF rules in another video.
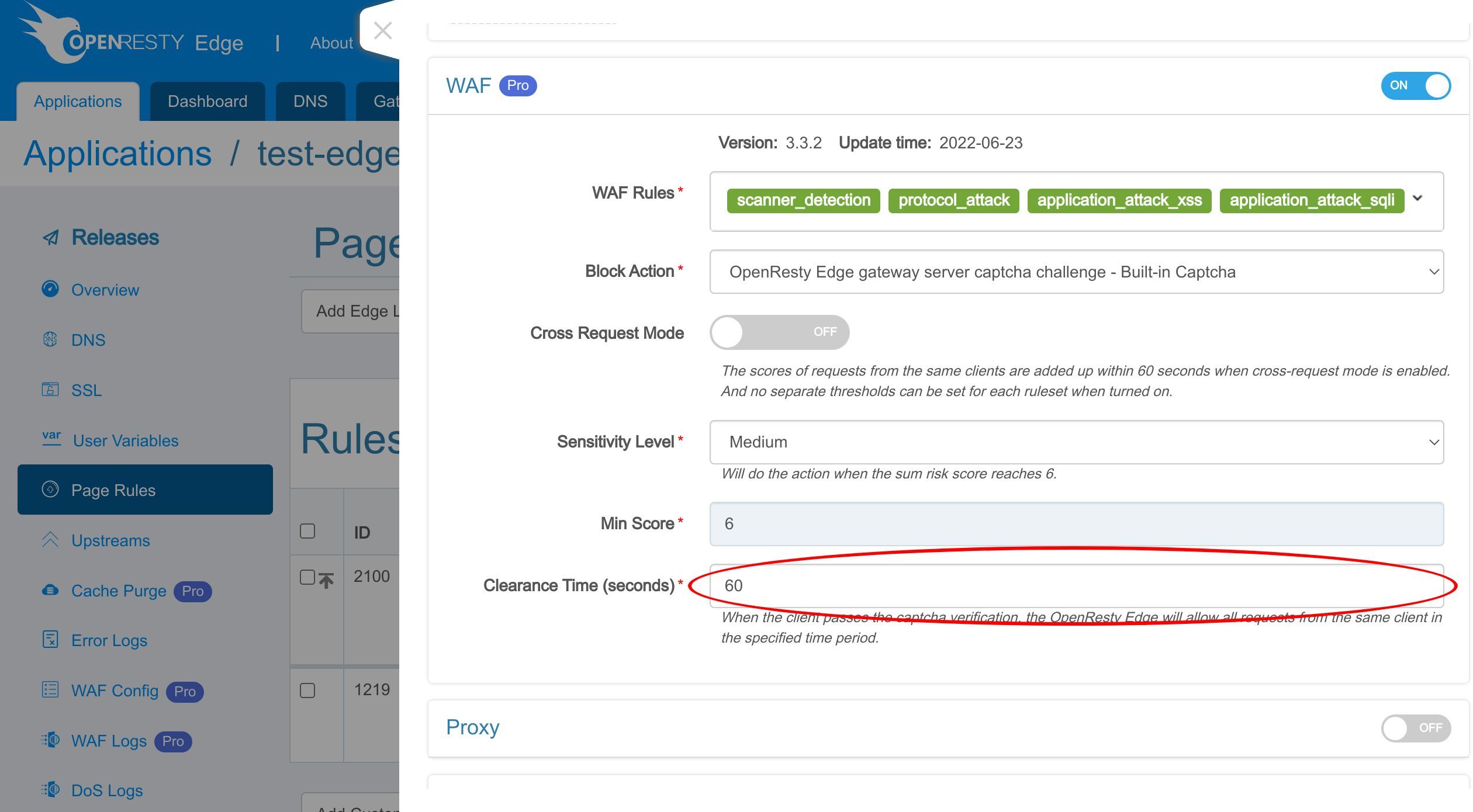
Let’s take a brief look at how to set up the OpenResty Edge built-in captcha in the WAF rules.
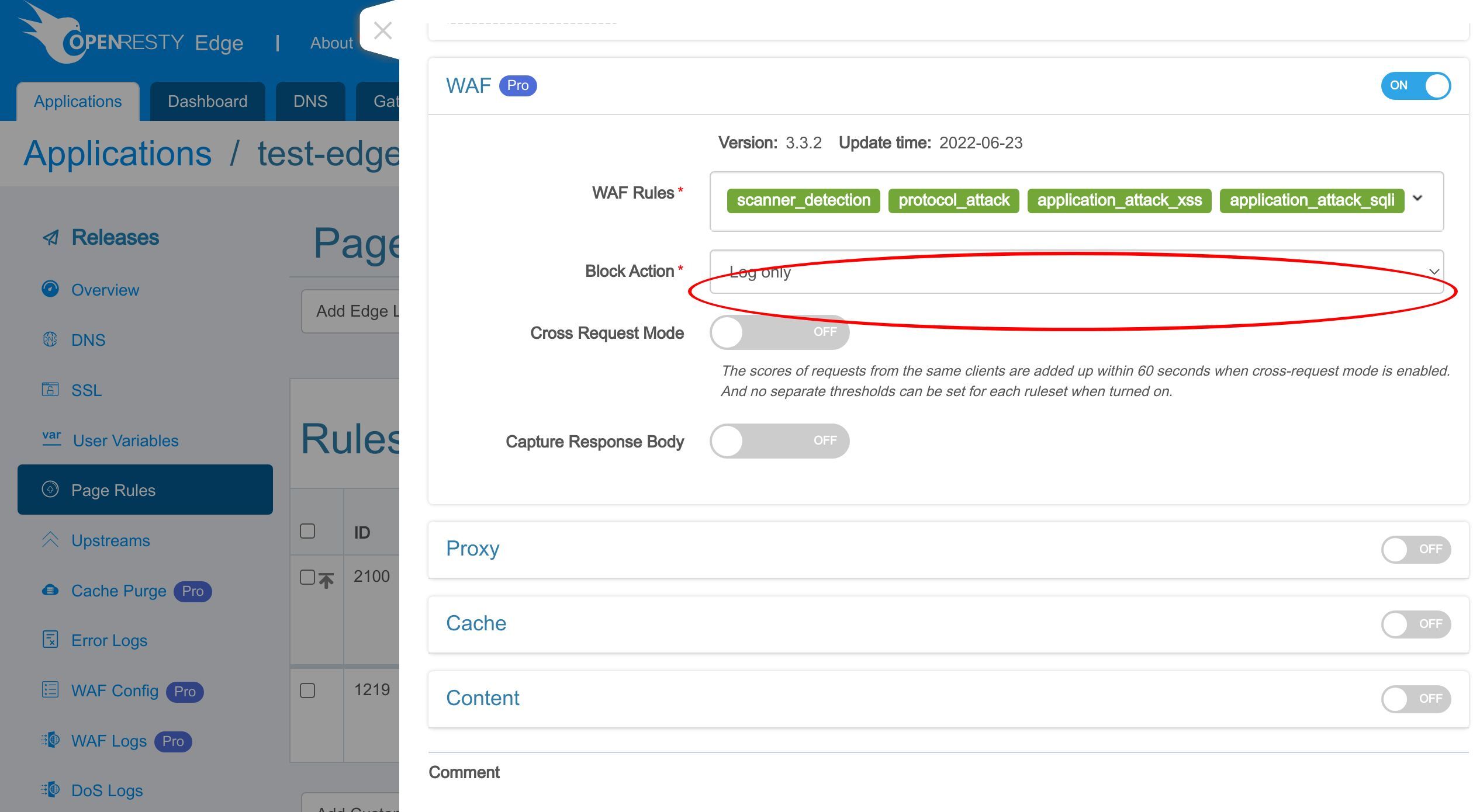
Let’s enable WAF.
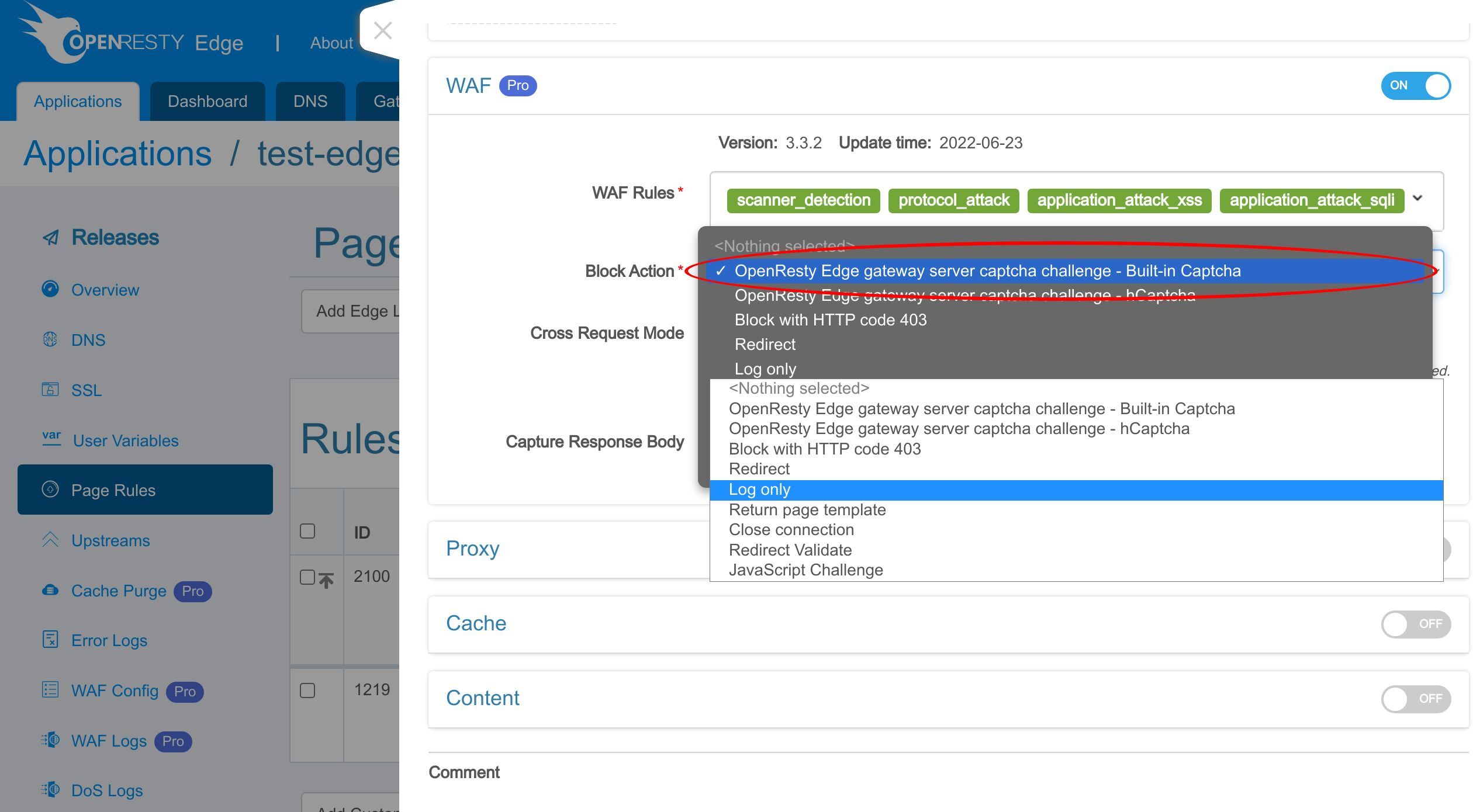
We can set the block action to the OpenResty Edge built-in Captcha.
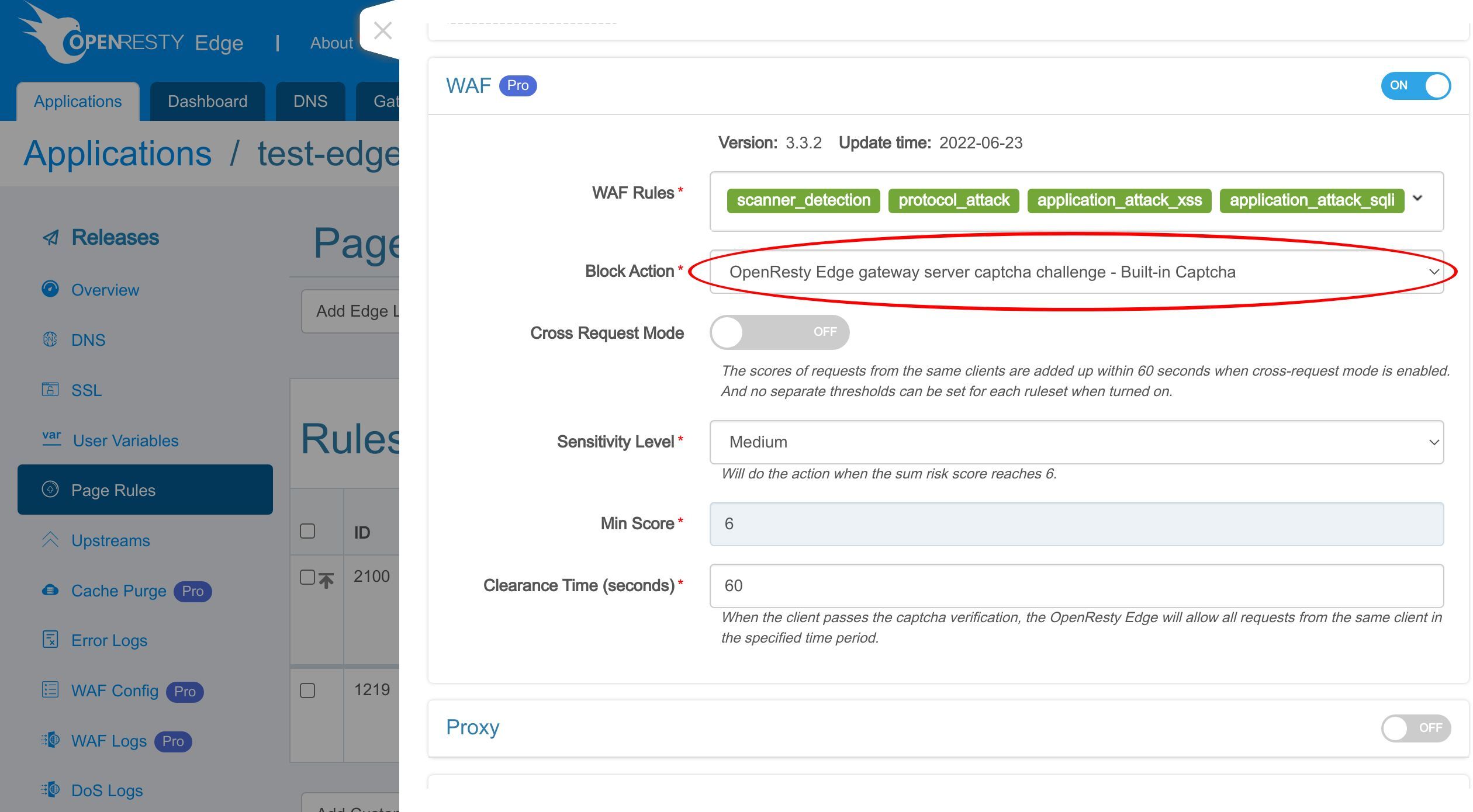
We selected the built-in captcha option.
As with the action we set before, we need to set a clearance time here. I won’t demonstrate it in detail here. You can go through it in a WAF rules-related video.
By the way, we also support the third-party captcha service hCaptcha. You can learn about it in the OpenResty Edge hCaptcha tutorial video.
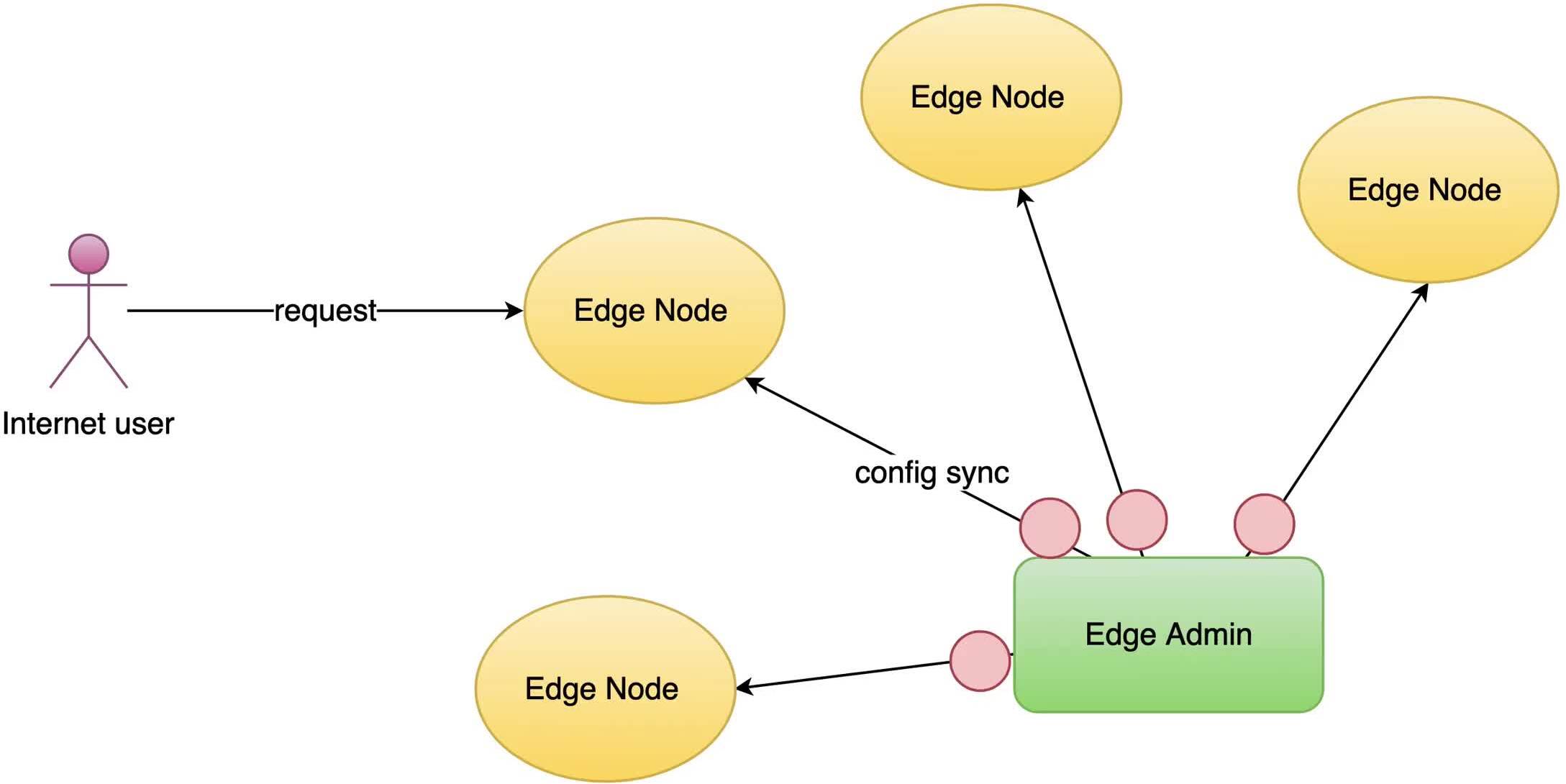
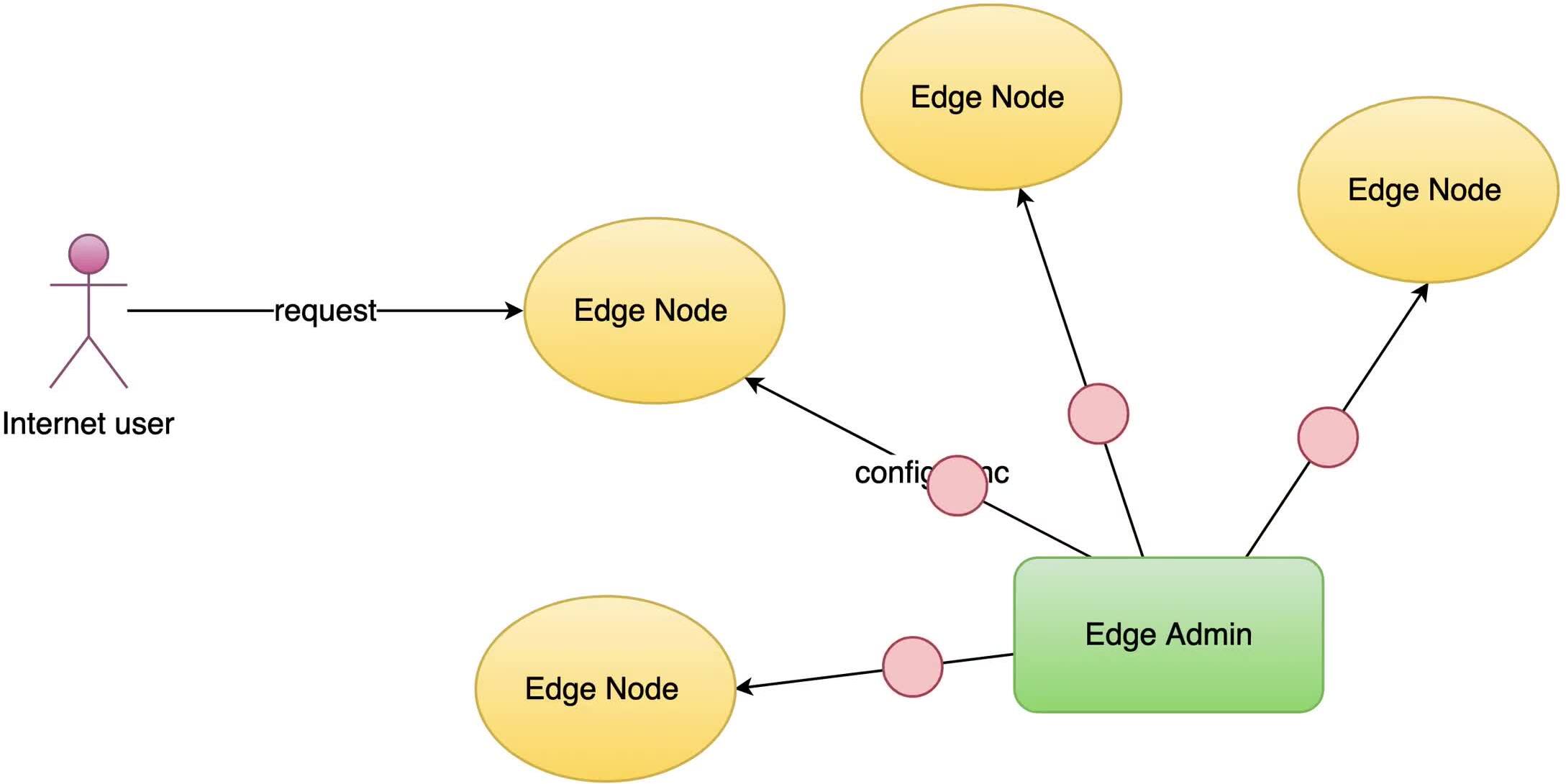
What is OpenResty Edge
OpenResty Edge is our all-in-one gateway software for microservices and distributed traffic architectures. It combines traffic management, private CDN construction, API gateway, security, and more to help you easily build, manage, and protect modern applications. OpenResty Edge delivers industry-leading performance and scalability to meet the demanding needs of high concurrency, high load scenarios. It supports scheduling containerized application traffic such as K8s and manages massive domains, making it easy to meet the needs of large websites and complex applications.
If you like this tutorial, please subscribe to this blog site and/or our YouTube channel. Thank you!
About The Author
Yichun Zhang (Github handle: agentzh), is the original creator of the OpenResty® open-source project and the CEO of OpenResty Inc..
Yichun is one of the earliest advocates and leaders of “open-source technology”. He worked at many internationally renowned tech companies, such as Cloudflare, Yahoo!. He is a pioneer of “edge computing”, “dynamic tracing” and “machine coding”, with over 22 years of programming and 16 years of open source experience. Yichun is well-known in the open-source space as the project leader of OpenResty®, adopted by more than 40 million global website domains.
OpenResty Inc., the enterprise software start-up founded by Yichun in 2017, has customers from some of the biggest companies in the world. Its flagship product, OpenResty XRay, is a non-invasive profiling and troubleshooting tool that significantly enhances and utilizes dynamic tracing technology. And its OpenResty Edge product is a powerful distributed traffic management and private CDN software product.
As an avid open-source contributor, Yichun has contributed more than a million lines of code to numerous open-source projects, including Linux kernel, Nginx, LuaJIT, GDB, SystemTap, LLVM, Perl, etc. He has also authored more than 60 open-source software libraries.